Security testing is not optional for Virtual Asset Service Providers (VASPs) operating under VARA’s regulatory framework in Dubai. The VARA Technology and Information Rulebook establishes specific, measurable testing requirements that go well beyond what most VASPs are accustomed to from other jurisdictions. Annual penetration tests, quarterly vulnerability assessments, mandatory smart contract audits, and the possibility of Threat-Led Penetration Testing (TLPT) on critical systems - these are not suggestions. They are licence conditions.
This article unpacks the full scope of VARA’s testing and audit requirements. We will walk through Part I Section E (Testing and Audit), Schedule 1 Risk Category 2 (which covers security testing as one of its 13 control areas), and Schedule 1 Risk Category 5 (digital operational resilience testing). We will cover what tests you must run, how often, who can perform them, and what VARA expects to see in your reports.
Whether you are a CISO building your annual testing programme, a compliance officer preparing for a VARA inspection, or an external assessor scoping a VASP engagement, this is the comprehensive reference.
Where Testing Requirements Sit in the VARA Framework

VARA’s testing obligations come from three interconnected sources within the Technology and Information Rulebook. Understanding where each requirement originates is essential for building a compliant testing programme.
These three sources are complementary, not alternative. A VASP’s testing programme must satisfy all three. In practice, this means your annual testing calendar will include traditional infrastructure pen tests, application security assessments, smart contract audits, vulnerability scanning, and potentially TLPT - each with specific scope, frequency, and provider requirements.
Annual Penetration Testing: Scope, Methodology, and Provider Requirements

Part I Section E of the Technology and Information Rulebook mandates that VASPs conduct annual penetration testing of their systems. This is not a cursory scan - VARA expects a comprehensive, methodology-driven assessment conducted by an independent third party.
The scope must cover:
External Infrastructure
Internet-facing systems, APIs, web applications, mobile applications, cloud infrastructure, and all services accessible from the public internet. This includes exchange frontends, wallet APIs, and trading interfaces.
Internal Infrastructure
Internal networks, administrative interfaces, database servers, key management systems, and HSM management interfaces. Assume-breach testing from within the network perimeter is expected, not just external probing.
Application Security
Trading platforms, wallet management applications, KYC/AML systems, and administrative portals. This must include authentication, authorisation, session management, input validation, and business logic testing specific to virtual asset operations.
Custody and Signing Infrastructure
HSMs, signing services, multi-sig infrastructure, transaction approval workflows, and key management systems. This is where Schedule 1 Risk Category 2’s “Security Testing” control area intersects directly with the pen testing requirement.
Key requirement: Penetration tests must be conducted by independent third parties. VARA is explicit about independence - the testing provider must not be the same firm that designed, built, or manages the systems being tested. Internal security teams can supplement but not substitute for external testing.
Methodology expectations: VARA does not prescribe a specific testing methodology, but expects alignment with recognised standards. In practice, this means OWASP Testing Guide for web applications, PTES (Penetration Testing Execution Standard) or CREST methodology for infrastructure, and blockchain-specific testing frameworks for custody and smart contract systems. Your testing provider should document their methodology in the report, and it must be reproducible.
Reporting requirements: Pen test reports must include an executive summary suitable for board and VARA review, detailed technical findings with severity ratings (CVSS or equivalent), proof of exploitation where applicable, and a prioritised remediation plan with agreed timelines. VARA may request copies of pen test reports during inspections, so ensure your engagement contract permits disclosure to the regulator.
Quarterly Vulnerability Assessments

Beyond annual penetration testing, VARA expects VASPs to conduct regular vulnerability assessments - at minimum quarterly. These are distinct from pen tests: vulnerability assessments are systematic scans to identify known vulnerabilities, misconfigurations, and missing patches across your environment. They are broader but shallower than pen tests.
A compliant vulnerability assessment programme must include:
- Authenticated scanning: Scans should use authenticated credentials where possible to identify vulnerabilities that would not be visible to an unauthenticated scanner. This is particularly important for web applications and administrative interfaces.
- Full asset coverage: Every system in scope (servers, containers, cloud instances, databases, network devices, and endpoints) must be included. Shadow IT and unmanaged assets are common blind spots that VARA will ask about.
- Remediation tracking: Identifying vulnerabilities is only half the requirement. VASPs must track remediation with defined SLAs based on severity - critical vulnerabilities within 48 hours, high within 7 days, medium within 30 days, and low within 90 days (or provide documented risk acceptance).
- Trend analysis: VARA expects VASPs to track vulnerability trends over time. Are you finding fewer critical vulnerabilities each quarter? Is your mean time to remediation improving? This data demonstrates security maturity.
“A VASP that runs quarterly vulnerability scans but has no evidence of remediation tracking is worse off than one that runs less frequent scans with rigorous follow-through. VARA cares about the complete cycle: identify, prioritise, remediate, verify, and report. Scanning without remediation is compliance theatre.”
Smart Contract Audit Requirements

Smart contract security sits at the intersection of Part I Section E and Schedule 1 Risk Category 2. If your VASP deploys, manages, or materially relies on smart contracts - whether for token issuance, DeFi integrations, staking, automated market making, or custody logic - VARA requires independent security audits of those contracts.
The smart contract audit requirements are specific:
Pre-Deployment Audit
Every smart contract must undergo an independent security audit before deployment to production. The audit must cover common vulnerability classes including reentrancy, integer overflow/underflow, access control flaws, oracle manipulation, flash loan attack vectors, front-running vulnerabilities, and logic errors. The audit report must be completed by a qualified third-party firm with demonstrated smart contract security expertise.
Post-Update Re-Audit
Any material change to a smart contract - whether through an upgrade proxy, parameter modification, or redeployment - triggers a requirement for re-audit. The scope of the re-audit can be limited to the changed components and their interactions, but the auditor must confirm that existing security properties have not been degraded. VASPs that use upgradeable proxy patterns must be particularly vigilant here.
Formal Verification
For high-value contracts - particularly those controlling client assets, managing custody logic, or handling significant TVL (Total Value Locked) - VARA expects VASPs to consider formal verification. While not an absolute mandate for all contracts, VARA has indicated in its guidance that formal verification is a strong indicator of security maturity. Mathematical proofs that critical invariants hold under all possible inputs provide a level of assurance that testing alone cannot achieve.
Ongoing Monitoring
Smart contract audits are point-in-time assessments. VARA also expects VASPs to implement ongoing monitoring of deployed contracts - transaction anomaly detection, access pattern monitoring, and alerts for unusual interactions. This connects to the broader operational resilience requirements in Risk Category 5. A contract that was secure at deployment may become vulnerable due to changes in the broader ecosystem (new attack techniques, dependency vulnerabilities, or protocol-level changes).
Threat-Led Penetration Testing (TLPT)
VARA reserves the right to require Threat-Led Penetration Testing (TLPT) on critical systems. This is not a standing requirement for all VASPs - it is a discretionary power that VARA can exercise based on the risk profile, size, and systemic importance of the VASP. However, any VASP handling significant client assets, operating a major exchange, or providing custody services should plan for the possibility.
TLPT is fundamentally different from a standard penetration test. It is an intelligence-led, red team exercise conducted against live production systems, designed to simulate realistic adversary scenarios specific to the VASP’s threat landscape. The key differences are:
Important: Even if VARA has not yet required TLPT for your VASP, your readiness to execute one is a compliance differentiator. VASPs that can demonstrate they have TLPT-ready contracts, qualified provider relationships, and internal white team capabilities signal security maturity to the regulator.
Testing Provider Qualifications and TLPT Tester Criteria
VARA does not allow just anyone to conduct security testing on licensed VASPs. For standard penetration tests, the provider must be an independent third party with demonstrated expertise. For TLPT specifically, the requirements are significantly more stringent.
TLPT tester criteria under VARA:
- Reputation and track record: The testing firm must have an established reputation in threat-led and red team testing, with demonstrable experience in financial services or virtual asset environments.
- Technical capability: Testers must demonstrate deep technical expertise in the specific technologies used by the VASP - blockchain protocols, HSM systems, custody architectures, DeFi protocols, and smart contract platforms.
- Certification: Individual testers must hold recognised offensive security certifications. While VARA does not prescribe specific certifications, OSCP, OSCE, CREST CRT/CCT, or equivalent are the expected baseline. For blockchain-specific testing, additional credentials or demonstrated bug bounty track records may be relevant.
- Insurance: TLPT providers must carry adequate professional indemnity insurance to cover potential operational disruption during live testing. VARA has indicated that VASPs should verify the adequacy of this coverage before engagement.
- Independence: No conflicts of interest. The TLPT provider cannot be the same firm that provides ongoing security operations, managed detection and response, or security architecture consulting to the VASP.
Practical guidance: For annual pen tests, we recommend maintaining a rotation of at least two qualified testing providers. Using the same firm every year creates familiarity bias - a fresh set of eyes often finds vulnerabilities that a previous tester normalised. VARA views provider rotation as a sign of testing programme maturity.
Schedule 1 Risk Category 5: Digital Operational Resilience Testing
Risk Category 5 broadens the testing lens beyond pure security testing to encompass digital operational resilience. This includes testing the VASP’s ability to withstand, respond to, and recover from operational disruptions - whether caused by cyberattacks, infrastructure failures, or third-party outages.
The testing areas under Risk Category 5 include:
Disaster Recovery Testing
Annual DR tests covering full system recovery, RTO/RPO validation, data integrity verification post-recovery, and failover to backup systems. For VASPs, this must include blockchain node recovery, wallet restoration, and key material availability at the backup site.
Business Continuity Testing
Tabletop exercises and simulation tests covering scenarios such as exchange outages during high-volatility periods, custody system failures, key compromise events, blockchain network forks, and third-party provider outages. These tests should involve cross-functional teams including operations, compliance, legal, and senior management.
Scenario-Based Testing
VASPs must design and execute tests based on realistic threat scenarios. Examples include: a state-sponsored APT targeting custody keys, a smart contract exploit draining a DeFi integration, a ransomware attack on operational infrastructure, or an insider threat scenario. Scenarios should be updated annually based on the evolving threat landscape.
Third-Party Resilience
Testing the VASP’s resilience when critical third parties fail. This includes cloud provider outages, blockchain node provider failures, banking partner disruptions, and KYC/AML provider unavailability. VASPs must demonstrate they can continue critical operations or gracefully degrade service during third-party disruptions.
Building a VARA-Compliant Annual Testing Calendar
Pulling all requirements together into a coherent annual testing programme is where many VASPs struggle. Here is a practical calendar that satisfies Part I Section E, Risk Category 2 Security Testing, and Risk Category 5 Resilience Testing:
“The biggest mistake VASPs make is treating security testing as a point-in-time compliance exercise rather than a continuous programme. VARA expects a testing cadence that reflects the dynamic threat landscape. Your testing programme should evolve as your attack surface evolves.”
Six Common Compliance Failures in VARA Security Testing
1. Scope exclusions on custody systems. Some VASPs exclude HSMs, signing infrastructure, or key management systems from pen test scope due to operational risk concerns. VARA expects these systems to be in scope. If live testing is too risky, negotiate a controlled testing approach with your provider - but do not exclude them entirely.
2. No evidence of remediation. Having pen test reports that identify critical and high vulnerabilities, with no documented evidence that those vulnerabilities were remediated and verified. VARA will check for remediation evidence, including re-test results confirming findings are closed.
3. Smart contracts deployed without audit. Deploying a new smart contract or making material changes to an existing one without an independent security audit. Even “minor” changes can introduce vulnerabilities. VARA expects audit coverage proportional to the risk.
4. Using the same pen test provider for 3+ years. Without rotation, testing becomes predictable and blind spots accumulate. VARA views long-term single-provider relationships as a weakness in the testing programme.
5. No vulnerability trending. Running quarterly scans but not tracking trends. VARA expects to see quarter-over-quarter metrics: total vulnerabilities, mean time to remediation, open critical/high findings, and age of unresolved issues. Without trending data, you cannot demonstrate improvement.
6. DR tests that never fail. If your disaster recovery tests always succeed perfectly, you are not testing aggressively enough. VARA is sophisticated enough to recognise that real DR exercises should surface issues. A test that reveals gaps and leads to improvements is more valuable than a scripted exercise that demonstrates nothing.
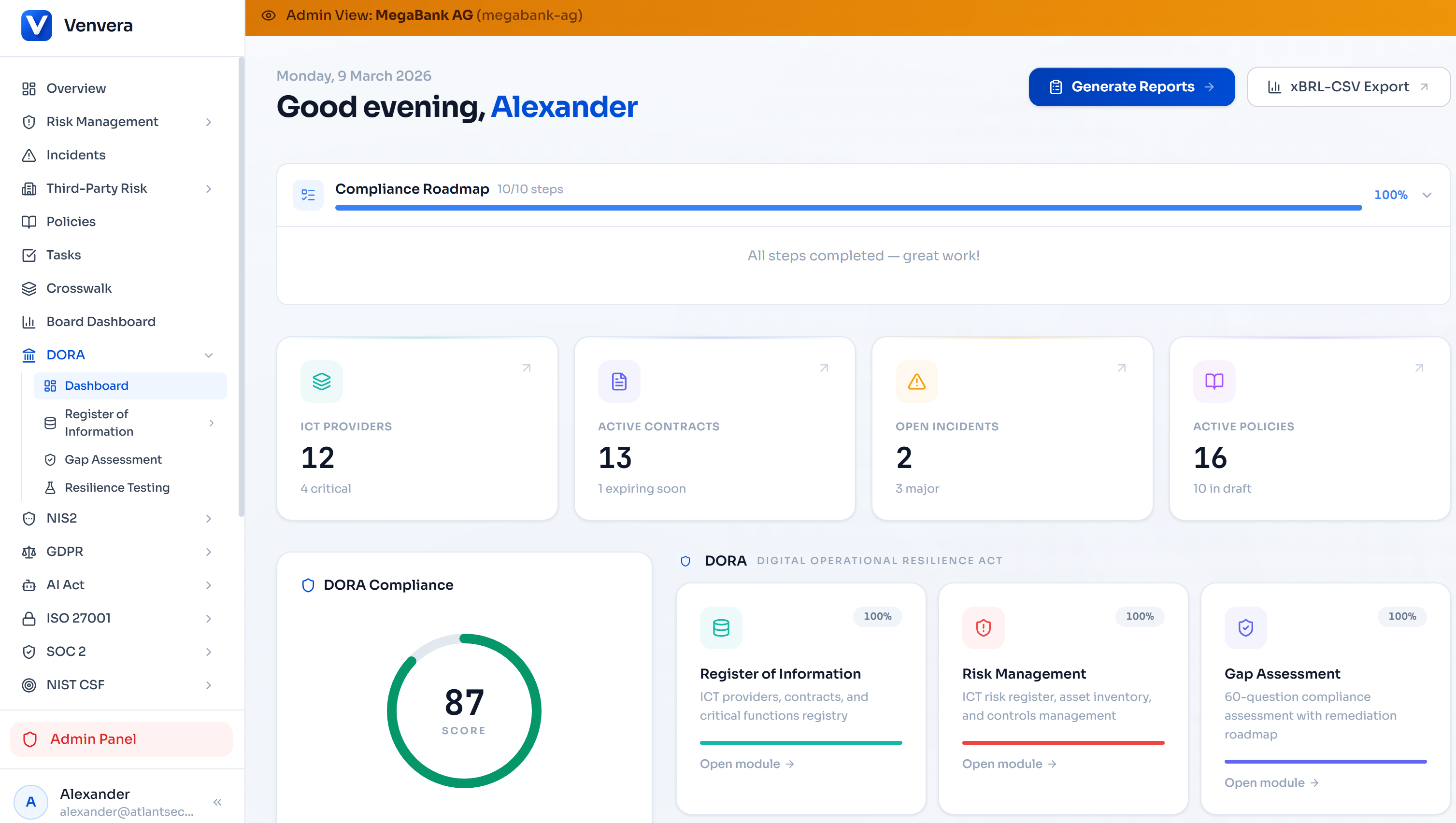
How Venvera Supports VARA Testing Compliance
Managing a VARA-compliant testing programme involves coordinating multiple testing streams, tracking findings across different assessment types, monitoring remediation timelines, and maintaining evidence for regulatory inspection. This requires structured tooling, not spreadsheets.
Venvera’s compliance platform provides purpose-built capabilities for VARA testing and audit compliance:
- Testing Programme Register: Maintain a structured register of all security testing activities - pen tests, vulnerability assessments, smart contract audits, DR exercises, and TLPT engagements - with status tracking, scheduling, and automated reminders.
- Findings Management: Centralise findings from all testing streams in a single, searchable repository. Assign severity, ownership, and remediation timelines. Track closure with re-test verification evidence.
- Vulnerability Trending: Automated dashboards showing quarter-over-quarter vulnerability metrics, MTTR trends, and open finding aging - exactly the data VARA expects to see during inspections.
- Smart Contract Audit Tracker: Log every smart contract audit, link it to the specific contract version and deployment, and track any post-audit remediation. Evidence that every deployed contract was audited is available at a click.
- Evidence Repository: Store pen test reports, vulnerability scan outputs, DR exercise records, and TLPT documentation in a structured evidence library with version control and access logging.
- Risk Integration: Link testing findings to your broader risk register, mapping vulnerabilities to specific business functions, third-party providers, and compliance obligations.
Venvera connects your testing programme to your broader VARA compliance posture - linking testing findings to Schedule 1 control assessments, risk registers, and regulatory reporting. One platform, complete visibility.
Testing Is Not Optional - Build the Programme Now
VARA’s testing and audit requirements represent one of the most comprehensive security testing frameworks in the global virtual asset regulatory landscape. The combination of annual pen tests, quarterly vulnerability assessments, mandatory smart contract audits, operational resilience testing, and discretionary TLPT creates a multi-layered assurance model that leaves little room for complacency.
The VASPs that will thrive under this framework are those that treat security testing as a continuous programme rather than an annual obligation. Regular testing, rigorous remediation tracking, trend analysis, and tested incident response procedures are not just compliance requirements - they are the operational foundation of a trustworthy virtual asset business.
Dubai’s ambition to be a global hub for virtual assets is predicated on regulatory credibility. VARA’s testing requirements are a significant part of that credibility. VASPs that invest in robust, well-documented testing programmes will be better positioned for licence renewals, regulatory inspections, and institutional client confidence. The investment pays dividends far beyond compliance.
References & Legal Basis
- VARA Technology and Information Rulebook - Part I, Section E (Testing and Audit)
- VARA Technology and Information Rulebook - Schedule 1, Risk Category 2 (Security Testing control area)
- VARA Technology and Information Rulebook - Schedule 1, Risk Category 5 (Digital Operational Resilience Testing)
- OWASP Testing Guide v4.2 - Web Application Security Testing Methodology
- CREST - Penetration Testing Procurement Guide and Tester Certification Standards
- Dubai Virtual Assets Regulatory Authority (VARA) - Established under Dubai Law No. 4 of 2022
Published
March 2026
Category
VARA Compliance
Reading Time
13 minutes
Audience
CISO, CTO, Compliance Officers, Security Teams