If you operate a Virtual Asset Service Provider (VASP) in Dubai, you already know that VARA - the Dubai Virtual Assets Regulatory Authority - has published some of the most technically prescriptive crypto regulations anywhere in the world. But when it comes to cryptographic key and wallet management, the requirements go deeper than most VASPs realise. Part I Section D of the Technology and Information Rulebook, combined with Schedule 1 Risk Category 2, establishes a level of operational rigour that many traditional financial regulators have not yet articulated.
This article breaks down exactly what VARA expects from your key management and wallet infrastructure. We will move through key generation, storage, wallet creation, multi-signature architectures, key compromise response, and the audit logging requirements that tie everything together. Whether you are a CISO designing your custody architecture, a compliance officer preparing for a VARA inspection, or a CTO evaluating HSM vendors, this is the technical reference you need.
One warning before we begin: VARA does not treat these requirements as aspirational. Non-compliance can result in licence conditions, restrictions on activity, or enforcement action. The regulator has been clear that VASPs in Dubai will be held to the highest standards of key management, and their inspection methodology reflects it.
Where Key Management Sits in the VARA Rulebook

VARA’s regulatory framework is structured across multiple rulebooks. Key and wallet management obligations primarily stem from two sources:
- Part I, Section D - Cryptographic Key and Wallet Management: This is the primary normative text. It establishes the overarching obligations around key lifecycle management, wallet operations, personnel controls, and audit requirements.
- Schedule 1, Risk Category 2 - Technical Standards: This schedule provides the detailed technical control requirements. It covers 13 specific areas including key generation, wallet creation, key storage security, smart contract security, multi-signature security, transaction verification, key compromise response, key holder management, authentication controls, developer workstations, security testing, unauthorised recovery, and audit logging.
The two must be read together. Section D tells you what you must do; Schedule 1 Risk Category 2 tells you how and to what standard. Attempting compliance with one while ignoring the other is a common mistake we see in VASP licence applications and renewal audits.
Key principle: VARA explicitly states that no single point of failure may exist in the key management process. This is the design philosophy that runs through every requirement in Section D. If any single person, system, or location can unilaterally move client assets or compromise key material, your architecture fails the test.
Key Generation: HSMs, Entropy, and Ceremony Requirements

Key generation is the foundation of your entire custody architecture. If keys are generated poorly, no amount of downstream security can compensate. VARA’s Schedule 1 Risk Category 2 treats key generation as the first control domain, and for good reason.
The requirements break down into several areas:
Hardware Security Modules (HSMs)
VARA expects key generation to occur within a secure cryptographic boundary, and in practice this means HSMs. While the rulebook does not name specific vendors, it requires that key generation hardware be tamper-resistant, that key material never exist in plaintext outside the HSM boundary, and that the entropy source meet recognised cryptographic standards (NIST SP 800-90A/B or equivalent). If you are generating keys in software on a general-purpose server, you will not pass a VARA inspection. The regulator has been clear in its guidance that HSMs (whether on-premises or cloud HSMs from AWS CloudHSM, Azure Dedicated HSM, or equivalent) are the expected standard for licensed VASPs.
Entropy and Randomness
The quality of random number generation is explicitly called out. VASPs must demonstrate that their key generation process uses a cryptographically secure random number generator (CSRNG) with sufficient entropy. For blockchain key pairs, this typically means at least 256 bits of entropy from a hardware-backed source. VARA expects documentation of the entropy source, evidence of entropy testing (e.g., NIST SP 800-22 statistical test suites), and a clear audit trail showing that the same entropy source is consistently used.
Key Ceremony Procedures
Key generation for custody wallets should follow a formal key ceremony process. VARA expects documented procedures covering: the physical environment (a secure, access-controlled room), the personnel involved (separation of duties - no single individual should be able to generate a complete key), the hardware used, and tamper-evident packaging for any key components generated. Key ceremonies must be witnessed, logged, and the logs retained. If you have operated PKI key ceremonies before, the concept is familiar; the application to blockchain custody is the same discipline applied to a different cryptographic context.
Practical tip: Document your key generation process as a step-by-step runbook with photographs. VARA inspectors will want to see not just that you have a policy, but that you have evidence of the policy being followed. A well-documented key ceremony with witness signatures, timestamped photographs, and serial numbers of hardware used is worth more than a 50-page policy document.
Key Storage: HSMs, Component Separation, and Backup Requirements

VARA’s most distinctive requirement in key storage is the explicit statement that keys stored online are not sufficient alone for authorising transactions. This is a deliberate architectural constraint. It means that a hot wallet alone - no matter how well-secured - cannot be the sole signing mechanism for customer transactions. There must be an offline or out-of-band component in the signing process.
The implications for custody architecture are significant:
“The most common architectural failure we see in VARA licence applications is an over-reliance on hot wallets. VARA is explicit: online keys alone are insufficient. If your signing architecture does not include an offline or out-of-band approval mechanism, you are non-compliant by design, not by accident.”
Wallet Creation: Separation of Duties and Tamper-Evident Processes

VARA requires VASPs to follow “industry best practices” for wallet management, which the regulator has defined through Schedule 1 Risk Category 2’s Wallet Creation controls. In practice, this means:
Separation of Duties
No single individual should be able to create a wallet, fund it, and authorise transactions from it. Wallet creation must involve at least two personnel, with the process documented and approved by a supervisor. This prevents both insider fraud and single-point-of-failure risk.
Tamper-Evident Processes
Wallet creation processes must include tamper-evident controls. This means sealed environments for key ceremony components, serialised tamper-evident bags for key shards, and documented chain-of-custody for all materials involved in wallet generation. If a seal is broken, there must be a documented incident response.
Wallet Segregation
Client assets must be segregated from VASP proprietary assets. VARA requires clear, auditable separation - different wallet addresses at minimum, and ideally different key hierarchies. The commingling of client and proprietary funds is a serious compliance failure that can result in enforcement action.
Audit Logging
Every wallet creation event must be logged with immutable audit trails. VARA specifically requires audit logs of all key access changes, wallet creation events, and any modifications to wallet configurations. Logs must be tamper-resistant and retained for the period specified by VARA (aligned with record-keeping obligations).
A common failure mode we encounter is VASPs that automate wallet creation without human oversight for high-value or custody wallets. While automated wallet generation is appropriate for low-value operational wallets (e.g., transaction processing intermediaries), custody wallets holding client assets require the full ceremony-grade process described above.
Multi-Signature Security: The M > N/2 Rule
VARA’s multi-signature requirements are among the most specific in any virtual asset regulatory framework globally. Schedule 1 Risk Category 2 establishes a clear mathematical threshold: in any multi-signature arrangement, the number of required signers (M) must be greater than half the total number of keyholders (N). In other words, M > N/2.
What this means in practice:
This rule also applies to MPC (Multi-Party Computation) threshold signature schemes, which are increasingly popular as an alternative to native multi-sig. If you use MPC-TSS, the threshold must still satisfy M > N/2. VARA does not distinguish between on-chain multi-sig and MPC-TSS - the principle of majority-required signing applies equally.
Warning: A 2-of-4 multi-sig configuration is non-compliant under VARA, even though it is common in the industry. The same applies to 1-of-3 or 2-of-5 with an administrative override. Any configuration where a minority of keyholders can authorise transactions fails the M > N/2 test.
Key Compromise Response Plans
Schedule 1 Risk Category 2 includes “Key Compromise Response” as a dedicated control area. VARA does not simply expect you to have an incident response plan that mentions key compromise - it expects a specific, tested, standalone key compromise response procedure that can be executed under pressure.
Your key compromise response plan must address:
- Detection: How will you detect a key compromise? This includes monitoring for unauthorised transaction attempts, anomalous signing patterns, HSM tamper alerts, and reports from keyholder personnel. Define specific triggers that initiate the response.
- Immediate revocation: VARA requires “immediate revocation procedures.” This means pre-established technical mechanisms to disable compromised keys or wallets within minutes, not hours. For multi-sig wallets, this may mean rotating out the compromised keyholder and migrating to a new wallet address.
- Asset migration: A documented procedure for moving client assets from a potentially compromised wallet to a new, clean wallet with freshly generated keys. This must be executable under emergency conditions and should include pre-signed transactions or emergency signing procedures.
- Communication: Internal escalation procedures, VARA notification requirements, and client communication templates. VARA expects to be notified promptly of any key compromise event.
- Post-incident review: Root cause analysis, lessons learned, and control improvements. VARA will expect evidence that you have conducted a thorough investigation and implemented changes to prevent recurrence.
Best practice: Run a tabletop exercise of your key compromise response at least twice per year. Include your custody team, CISO, legal counsel, and a representative from senior management. Document the exercise and its findings. VARA inspectors will ask for evidence that your response plan has been tested, not just written.
Key Holder Management and Authentication Controls
VARA dedicates specific attention to the human element of key management. Schedule 1 Risk Category 2 covers both “Key Holder Management” and “Authentication Controls” as separate control domains. The requirements include:
Formal Onboarding and Offboarding
VARA requires formal, documented procedures for onboarding new keyholders and offboarding departing ones. Onboarding must include background checks, training on key management procedures, and a witnessed key assignment ceremony. Offboarding must include immediate revocation of all key access, rotation of any keys the departing individual had access to, and a formal attestation that all key material has been returned or destroyed. The offboarding process must be executable within 24 hours of a termination decision.
Quarterly Access Audits
VARA requires quarterly audits of all personnel with access to key management systems, HSMs, key storage facilities, and signing infrastructure. These are not passive reviews - they must verify that each individual with access still requires it, that their access level is appropriate for their current role, and that no unauthorised access has been granted. The audit results must be documented and retained.
Authentication Controls
Access to key management systems must be protected by strong authentication - at minimum multi-factor authentication (MFA), and for the most critical systems (HSM administration, signing infrastructure), VARA expects hardware-based authentication tokens. Password-only access to any system that interacts with key material is non-compliant. Biometric factors combined with hardware tokens are recommended for custody signing operations.
Developer Workstation Security
Schedule 1 includes “Developer Workstations” as a control area, recognising that developers with access to custody code, smart contracts, or signing infrastructure represent a significant risk vector. VASPs must implement hardened developer environments, code signing requirements, and access controls that prevent developers from accessing production key material. Development and testing must use separate key hierarchies from production.
Transaction Verification and Smart Contract Security
Key management does not exist in isolation - it serves the transaction lifecycle. VARA’s Schedule 1 Risk Category 2 includes both “Transaction Verification” and “Smart Contract Security” as control areas that directly intersect with key management.
Transaction verification requires that VASPs implement controls to verify the integrity and authenticity of every transaction before it is signed. This includes:
- Destination address validation (whitelisting, sanction screening)
- Transaction amount limits with tiered approval requirements
- Replay attack prevention
- Transaction payload verification before signing (what you see is what you sign)
- Velocity checks to detect abnormal transaction patterns
Smart contract security is particularly important for VASPs that deploy or interact with DeFi protocols, token contracts, or automated market makers. VARA requires:
- Independent security audits of all smart contracts before deployment
- Formal verification where feasible for high-value contracts
- Upgrade mechanisms with multi-sig governance (satisfying the M > N/2 rule)
- Monitoring for anomalous contract interactions post-deployment
- Emergency pause/kill-switch capabilities controlled by multi-sig
“Smart contract security and key management are two sides of the same coin. A perfectly managed key protecting a vulnerable smart contract is a liability, not an asset. VARA understands this, which is why both appear together in Schedule 1 Risk Category 2.”
Audit Logging and Unauthorised Recovery Prevention
The final two control areas in Schedule 1 Risk Category 2 - “Audit Logging” and “Unauthorised Recovery” - serve as the accountability layer for everything discussed above. Without comprehensive logging, compliance cannot be demonstrated. Without controls against unauthorised recovery, backup procedures become an attack vector.
Audit Logging Requirements
- All key generation events
- All key access and usage events
- All changes to key access permissions
- All wallet creation and modification events
- All transaction signing events
- All key rotation and destruction events
- All backup access and restoration events
- Tamper-resistant log storage with integrity verification
Unauthorised Recovery Prevention
- Backup recovery requires multi-party authorisation
- Recovery procedures documented and tested
- Recovery events trigger alerts to senior management
- Physical access controls on backup storage
- Backup integrity verification before restoration
- Separation between backup custodians and operational signers
- Time-locked recovery mechanisms where appropriate
- Post-recovery audit of all restored key material
The Five Most Common VARA Key Management Compliance Failures
Based on our experience working with VASPs preparing for VARA licensing and ongoing compliance, these are the failures we see most frequently:
1. Hot wallet-only architecture. Relying solely on online keys for transaction signing, without an offline or out-of-band approval component. This violates VARA’s core principle that online keys alone are insufficient.
2. Non-compliant multi-sig thresholds. Using 2-of-4, 1-of-3, or other configurations where M is not greater than N/2. Often inherited from pre-VARA architectures and never updated.
3. Missing or informal offboarding. When a keyholder leaves the organisation, their access is revoked from IT systems but key shares are not rotated and the wallet is not migrated. The departed employee effectively retains the ability to participate in signing.
4. Co-located backups. Key backups stored in the same physical location or accessible by the same personnel as the primary keys. VARA is explicit about backup separation.
5. Untested key compromise response. Having a written key compromise procedure that has never been tested through a tabletop exercise or simulation. VARA expects evidence of testing, not just documentation.
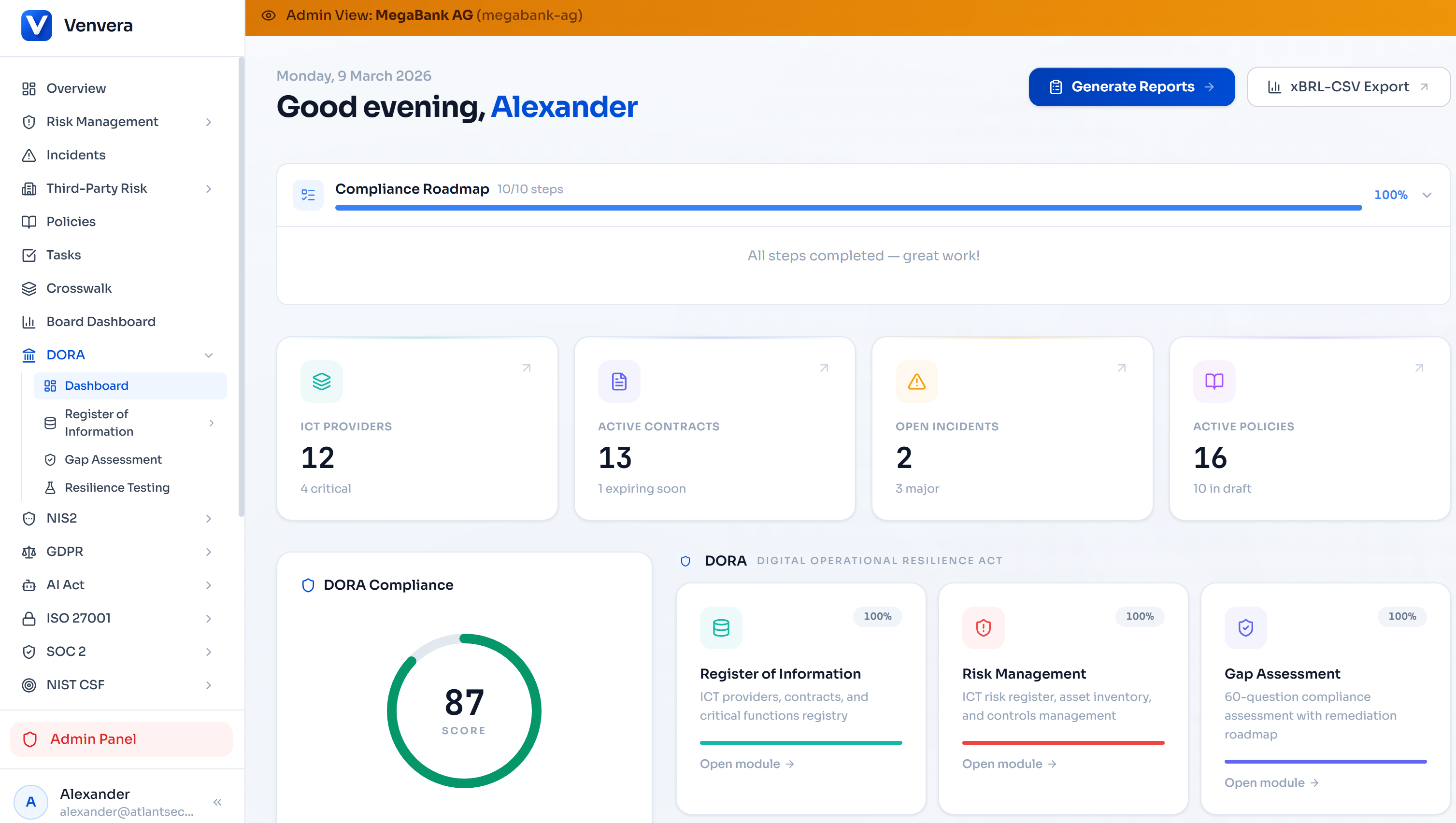
How Venvera Supports VARA Key Management Compliance
Managing VARA’s key management requirements across Schedule 1 Risk Category 2’s 13 control areas requires structured tracking, evidence management, and continuous monitoring. Spreadsheets and shared drives are not sufficient for the level of rigour VARA expects.
Venvera’s compliance platform provides purpose-built capabilities for VARA key management compliance:
- Control Mapping: Map each of the 13 Schedule 1 Risk Category 2 control areas to your internal controls, policies, and procedures. Track implementation status and identify gaps before VARA does.
- Evidence Repository: Store key ceremony records, access audit results, multi-sig configuration documentation, and compromise response exercise reports in a structured, searchable evidence library.
- Quarterly Access Review Automation: Set up quarterly review cycles for key management access, with automated reminders, approval workflows, and audit trail documentation.
- Gap Assessment: Run a structured gap assessment against VARA’s key management requirements, generating a prioritised remediation roadmap with clear ownership and timelines.
- Audit Trail: Maintain a tamper-proof log of all compliance activities, policy changes, and evidence submissions - essential for VARA inspections.
Venvera connects your VARA key management controls to your broader compliance posture - linking technical controls to risk assessments, incident management, and regulatory reporting across all applicable frameworks.
Key Management Is the Foundation of VARA Compliance
VARA’s cryptographic key and wallet management requirements are not theoretical guidelines - they are enforceable regulatory standards that VARA actively inspects against. The regulator has invested significantly in its technology supervision capability, and VASPs should expect detailed, technically informed scrutiny of their key management architecture during licensing, renewals, and ongoing inspections.
The fundamental design principles are clear: no single point of failure, majority-required signing, separation of duties, offline key components, and comprehensive audit logging. If your custody architecture was designed before VARA published its detailed requirements, now is the time to conduct a thorough gap assessment and remediate.
Dubai’s position as a global virtual asset hub depends on the credibility of its regulatory framework. VARA understands that key management failures are existential events for VASPs and their clients. The bar is high by design, and VASPs that meet it will have a genuine competitive advantage in institutional trust and client confidence.
References & Legal Basis
- VARA Technology and Information Rulebook - Part I, Section D (Cryptographic Key and Wallet Management)
- VARA Technology and Information Rulebook - Schedule 1, Risk Category 2 (Key Generation, Wallet Creation, Key Storage Security, Smart Contract Security, Multi-Signature Security, Transaction Verification, Key Compromise Response, Key Holder Management, Authentication Controls, Developer Workstations, Security Testing, Unauthorised Recovery, Audit Logging)
- NIST SP 800-90A/B - Recommendation for Random Number Generation Using Deterministic Random Bit Generators
- NIST SP 800-22 - Statistical Test Suite for Random and Pseudorandom Number Generators
- Dubai Virtual Assets Regulatory Authority (VARA) - Established under Dubai Law No. 4 of 2022
Published
March 2026
Category
VARA Compliance
Reading Time
12 minutes
Audience
CISO, CTO, Compliance Officers, Custody Architects