The Digital Operational Resilience Act became fully applicable on 17 January 2025. For the first twelve months, most National Competent Authorities operated in what the industry informally called "observation mode" - issuing guidance, collecting Register of Information submissions, and refining their supervisory frameworks. That grace period is over.
Beginning in Q1 2026, the ECB, BaFin, DNB, AMF, CSSF, and other NCAs across the EU have launched formal DORA supervisory assessments. These are not awareness exercises. They are structured, evidence-based reviews of your institution's ICT risk management framework, third-party arrangements, incident response capabilities, and resilience testing program - with real consequences for non-compliance.
This article walks you through the entire supervisory assessment lifecycle: who gets assessed first, what the process looks like in practice, what supervisors are specifically looking for, the penalty regime, and how different NCAs across Europe are approaching enforcement. Whether you have already received a notification letter or are preparing for the inevitable, this is the definitive guide to DORA enforcement in 2026.
Key Date: Q1 2026
The European Supervisory Authorities (EBA, ESMA, EIOPA) published their final Joint Guidelines on DORA supervisory review processes in December 2025. NCAs were required to integrate these into their national supervisory methodologies by 31 January 2026. Formal assessment cycles are now underway in at least 18 Member States.
Section 1
Who Gets Assessed First

NCAs do not assess every institution simultaneously. Under Articles 50-56 of DORA, supervisory authorities apply a risk-based prioritization model that determines the sequence and intensity of assessments. Understanding where your institution falls in this prioritization is critical for resource planning.
Risk-Based Selection Criteria
Systemic Importance
G-SIBs, O-SIIs, and entities classified as systemically important under CRD V are assessed in the first wave. The ECB's SSM institutions are already receiving notification letters.
ICT Incident History
Institutions that reported major ICT incidents under the ECB's cyber incident reporting framework or national schemes are flagged for priority assessment.
Third-Party Concentration
Entities with high dependency on a small number of critical ICT third-party providers - particularly those designated as CTPPs under Article 31 - are elevated in the queue.
Random & Thematic Selection
NCAs also conduct thematic reviews (e.g., cloud dependency in insurance) and random selections to ensure broad coverage across the supervised population.
The practical implication: if your institution has not been assessed yet, it does not mean you are exempt. It means you have time to prepare. NCAs have committed to reviewing the majority of significant institutions within the 2026-2027 supervisory cycle, with smaller entities following in subsequent waves based on the proportionality principle embedded in DORA's recitals.
"Supervisory authorities shall conduct their reviews in a manner that is proportionate to the size, complexity, and risk profile of the financial entity, while ensuring that all entities within scope are subject to adequate supervisory oversight."
- DORA Article 50(2), Supervisory Powers
Section 2
The Supervisory Assessment Process: A Detailed Walkthrough

DORA supervisory assessments follow a structured methodology that NCAs have refined over the past year. While specific timelines and procedures vary by jurisdiction, the core process follows five distinct phases. Understanding each phase allows you to allocate resources appropriately and avoid scrambling when the notification arrives.
Phase 1 - Notification & Scope Definition
The process begins with a formal notification letter from your NCA, typically sent 4-8 weeks before the assessment commences. This letter specifies the scope of the review (full DORA assessment or thematic focus), the anticipated timeline, and the initial document request list. The scope may cover your entire DORA compliance framework or focus on specific pillars - ICT risk management (Chapter II), incident reporting (Chapter III), resilience testing (Chapter IV), or third-party risk (Chapter V).
Typical timeline: 4-8 weeks advance notice. Response to initial document request: 2-3 weeks.
Phase 2 - Document Request & Desk Review
Supervisors request comprehensive documentary evidence before any on-site activity. This is where most institutions experience their first shock - the granularity far exceeds expectations. Typical requests include:
- Complete Register of Information (Art. 28) with all ICT providers, contractual arrangements, and sub-outsourcing chains
- ICT risk management framework documentation and approved policies (Art. 6-16)
- Resilience testing program, including TLPT reports and vulnerability assessment results (Art. 24-27)
- Incident classification procedures and historical incident reports filed (Art. 17-23)
- Board-level ICT risk reports and management body approval records (Art. 5)
- Business continuity and disaster recovery plans with evidence of testing
- ICT third-party contracts, exit strategies, and concentration risk analyses
- Training records demonstrating ICT risk awareness at all levels, including the management body
Phase 3 - On-Site Visits or Remote Assessments
Depending on risk profile, assessments involve on-site visits, remote deep-dives, or a combination. On-site visits typically last 3-5 days for significant institutions with a team of 3-6 specialist examiners. Remote assessments follow a similar structure via secure video conferencing with screen-sharing.
Supervisors will request live demonstrations of your ICT risk management tools, incident escalation workflows, and Register of Information systems. They want to see that your processes are operational, not merely documented.
Phase 4 - Interviews with Key Personnel
A distinctive feature of DORA assessments is the emphasis on management body accountability under Article 5. Supervisors conduct structured interviews with:
- Board members / management body: Demonstrating that ICT risk is a standing agenda item, that the board has approved the ICT risk management framework, and that members have received adequate training
- CTO / CIO: Technical architecture, resilience testing outcomes, change management processes
- CISO: Incident classification procedures, threat landscape assessments, security operations
- Chief Risk Officer: Integration of ICT risk into the overall risk management framework
- Compliance / DPO: Regulatory reporting processes, cross-regulation alignment (DORA-GDPR-NIS2)
- Third-party risk managers: Vendor assessment processes, contract monitoring, exit plan testing
These are not perfunctory conversations. Supervisors are trained to identify inconsistencies between documented policies and actual understanding at the operational level.
Phase 5 - Assessment Report & Findings
The NCA issues a formal assessment report within 6-12 weeks, categorizing findings by severity (critical, major, minor, observation) with remediation timelines. Institutions can respond to draft findings before finalization. Critical findings may trigger immediate remediation orders under Article 50(2)(f), while lesser findings allow 3-12 months for resolution.
The final report becomes part of your supervisory record and informs future supervisory intensity decisions - a poor assessment leads to more frequent and intrusive follow-up reviews.
Section 3
What Supervisors Are Looking For: Assessment Criteria

Based on the ESA Joint Guidelines and early NCA assessment frameworks, the following table maps what supervisors evaluate and what separates a satisfactory assessment from one that generates findings.
| Assessment Area | DORA Reference | Satisfactory ("Good") | Insufficient (Finding Issued) |
|---|---|---|---|
| Management body oversight | Art. 5 | Board formally approves ICT risk framework; standing agenda item with quarterly reporting; members have documented ICT training | No evidence of board-level ICT risk discussions; framework approved by IT without board sign-off; no training records |
| ICT risk management framework | Art. 6-16 | Documented framework with clear ownership, risk appetite statements, regular review cycles; integrated with enterprise risk management | Generic IT policies rebranded as "DORA framework"; no ICT risk appetite; policies not reviewed since pre-DORA era |
| Register of Information | Art. 28(3) | Complete, accurate RoI covering all ICT third-party providers; contractual arrangements mapped to business functions; maintained in exportable ESA format | Incomplete provider inventory; missing sub-outsourcing chains; unable to produce ESA-format export; data quality issues (missing LEIs, wrong entity codes) |
| Incident classification & reporting | Art. 17-23 | DORA-specific taxonomy implemented; classification thresholds defined and tested; reporting timelines met (4h/24h/72h); root cause analysis documented | Pre-DORA process not updated; classification based on subjective judgment; late or missing NCA notifications |
| Resilience testing program | Art. 24-27 | Risk-based testing covering critical ICT systems; TLPT performed where required; findings tracked to remediation; lessons fed back into risk assessments | Testing limited to annual pen test; no TLPT for entities meeting threshold; results not linked to risk management; prior findings unaddressed |
| Third-party risk management | Art. 28-30 | Due diligence for ICT providers; concentration risk analysed; exit strategies documented and tested; contracts aligned with Art. 30 | No exit strategies; contracts missing DORA clauses (audit rights, data location, subcontracting); concentration risk not assessed |
| Business continuity & DR | Art. 11-12 | BCP/DRP covers all critical functions; tested annually with documented results; RPO/RTO defined and validated; lessons incorporated | Plans exist on paper but untested; RPO/RTO not defined; last DR test over 12 months ago; test failures not addressed |
| ICT change management | Art. 9(4)(e) | Formal process with risk assessment, testing, rollback procedures; emergency change process defined; audit trail maintained | Informal or inconsistent processes; no pre-deployment risk assessment; emergency changes bypass all controls |
| Information sharing | Art. 45 | Participation in threat intelligence sharing; process for acting on shared intelligence; documented decision if not participating | No awareness of sharing obligations; no participation or rationale for non-participation |
| ICT asset management & classification | Art. 8 | Complete ICT asset inventory; classification by criticality; dependencies mapped; assets supporting critical functions identified | Incomplete inventory; no criticality classification; dependencies unknown; shadow IT not addressed |
Assessment Scoring Note
Most NCAs are using a maturity-based scoring model with four levels: non-existent (no evidence of compliance), initial (ad-hoc processes), defined (documented and implemented), and managed (actively monitored and continuously improved). Institutions scoring "non-existent" or "initial" on any core domain should expect critical or major findings requiring remediation within 3-6 months.
Section 4
Penalties, Remediation Orders, and Consequences

DORA gives NCAs significant enforcement powers under Articles 50-56. Unlike some regulations where penalties are a distant theoretical threat, DORA's enforcement framework was designed with teeth from the outset. The consequences of a poor supervisory assessment extend far beyond financial penalties.
Administrative Penalties
Member States have transposed penalty provisions with varying maximums. Some jurisdictions have set fines at €5 million or 1% of average daily turnover, with personal director liability up to €500,000. Penalties apply for inadequate ICT risk management, late incident reporting, and non-compliant third-party arrangements.
Public Censure
Under Article 54, NCAs may publish penalty decisions including the institution's identity. Clients, counterparties, and investors will see your institution failed a DORA assessment. For listed entities, this can directly impact share price and credit ratings.
Remediation Orders
NCAs can require specific remedial actions: cessation of non-compliant practices, appointment of qualified ICT risk officers, renegotiation of non-compliant contracts, and enhanced supervisory reporting during remediation.
Board Reporting Obligations
Assessment findings must be reported to the management body. In several jurisdictions, NCAs require written confirmation that the board has been briefed on findings within 30 days. For critical findings, supervisors may require the board to submit a remediation plan directly, elevating the issue beyond management to governance level.
Cascading Impact
A critical finding in one assessment domain often triggers expanded scrutiny in related areas. For example, an insufficient Register of Information signals potential weaknesses in third-party risk management, which in turn raises questions about concentration risk and exit planning. Supervisors are trained to follow these threads - a single critical finding can widen the scope and duration of the assessment significantly.
Section 5
How Different NCAs Are Approaching DORA Enforcement
DORA is a regulation (not a directive), meaning it is directly applicable across all Member States. However, supervisory approach and enforcement intensity vary significantly by jurisdiction. The following comparison reflects published NCA communications and industry intelligence as of early 2026.
| NCA | Jurisdiction | Enforcement Posture | Approach & Focus Areas | Key Observations |
|---|---|---|---|---|
| ECB (SSM) | Euro Area | Aggressive | Integrated DORA assessments into SREP methodology; ICT risk now a dedicated SREP module. Focus on RoI completeness, TLPT for significant institutions, third-party concentration. | First wave began January 2026 for ~113 directly supervised banks. Findings feed into Pillar 2 capital requirements. |
| BaFin | Germany | Aggressive | Building on established BAIT/VAIT/KAIT framework. BaFin views DORA as a strengthening of existing requirements. Emphasis on operational testing, outsourcing supervision, and incident reporting quality. | Published supervisory expectations Q4 2025. On-site assessments began February 2026. Known for short remediation timelines. |
| DNB | Netherlands | Structured | Phased approach starting with a self-assessment questionnaire, followed by risk-based selection for deep-dive reviews. Strong focus on cloud concentration risk and cross-border ICT dependencies. | Issued DORA readiness questionnaire Q4 2025. Results inform 2026 assessment scheduling. Collaborative tone but firm on deadlines. |
| AMF / ACPR | France | Structured | ACPR coordinating with AMF for cross-sectoral consistency. Emphasis on incident reporting processes and information sharing participation. Thematic review on cloud outsourcing planned for H2 2026. | Vocal about expectations via industry circulars. First formal assessments targeting large banks and insurers Q1-Q2 2026. |
| CSSF | Luxembourg | Phased | Proportionality-focused approach given Luxembourg's large fund management sector. Initial focus on significant credit institutions and payment service providers. Asset managers and fund administrators in second wave. | Published DORA FAQs for the fund industry. Recognizes smaller fund managers need more time to build capabilities. |
| CBI | Ireland | Structured | Strong operational resilience focus, building on existing Cross Industry Guidance. Particular attention to global technology firms providing ICT services to Irish-regulated entities. Emphasis on board accountability. | Integrated DORA into existing PRISM framework. Significant institutions assessed from Q1 2026. Known for enforcement follow-through. |
Cross-Border Implications
For institutions supervised across multiple jurisdictions, assessment timing and methodology may differ. The ECB coordinates with national NCAs through Joint Supervisory Teams, but less significant entities may face varying approaches. Divergence in enforcement intensity is expected throughout 2026 as NCAs build capabilities at different speeds.
Section 6
Preparing for a Supervisory Assessment: The Practical Checklist
Preparation is everything. Institutions that scramble to compile evidence after receiving a notification letter consistently receive worse assessment outcomes than those with standing readiness. The following checklist represents the minimum level of preparation you should have in place before an NCA comes knocking.
Assessment Readiness Checklist
1. Register of Information
Complete RoI with all providers, contractual arrangements, business function mappings, sub-outsourcing chains, and LEIs. Verify ESA-format export. Cross-reference against procurement records to identify missing providers.
2. ICT Risk Management Framework Documentation
Board-approved ICT risk management framework with all supporting policies (information security, access control, change management, BCP, incident management). Evidence of annual review with dates and signatories.
3. Board-Level Evidence Pack
Board minutes showing quarterly ICT risk discussions. Board-approved risk appetite statement. Management body training records. Board-level ICT risk dashboards.
4. Incident Response Readiness
DORA-specific classification matrix with quantitative thresholds. Documented NCA reporting workflow with escalation paths. Historical incident log with root cause analyses. Evidence of tabletop exercises.
5. Resilience Testing Evidence
Testing program aligned to Art. 24-27. TLPT results (if applicable). Vulnerability assessment reports with remediation tracking. BCP/DR test results with lessons learned fed back into risk assessments.
6. Third-Party Contracts & Exit Plans
All contracts reviewed for Art. 30 compliance (audit rights, data location, subcontracting, termination). Exit strategies for critical providers. Concentration risk analysis current.
7. Gap Assessment & Remediation Tracker
Internal gap assessment completed and documented. Remediation plan with owners, deadlines, and progress tracking. Demonstrating you know your gaps and have a plan to close them is often more valuable than claiming you have none.
8. Staff Readiness
Designated assessment coordinator. Pre-briefed CTO, CISO, CRO, and board members on their roles. Interview preparation for key personnel. Central document repository accessible to the assessment team.
"The institutions that perform best in supervisory assessments are not the ones with perfect compliance - they are the ones that can demonstrate they understand their own gaps, have a credible remediation plan, and can retrieve evidence quickly and completely. Supervisors recognize that DORA is still maturing. What they will not accept is ignorance or inaction."
- Former ECB supervisory examiner, speaking at a 2025 industry conference
Section 7
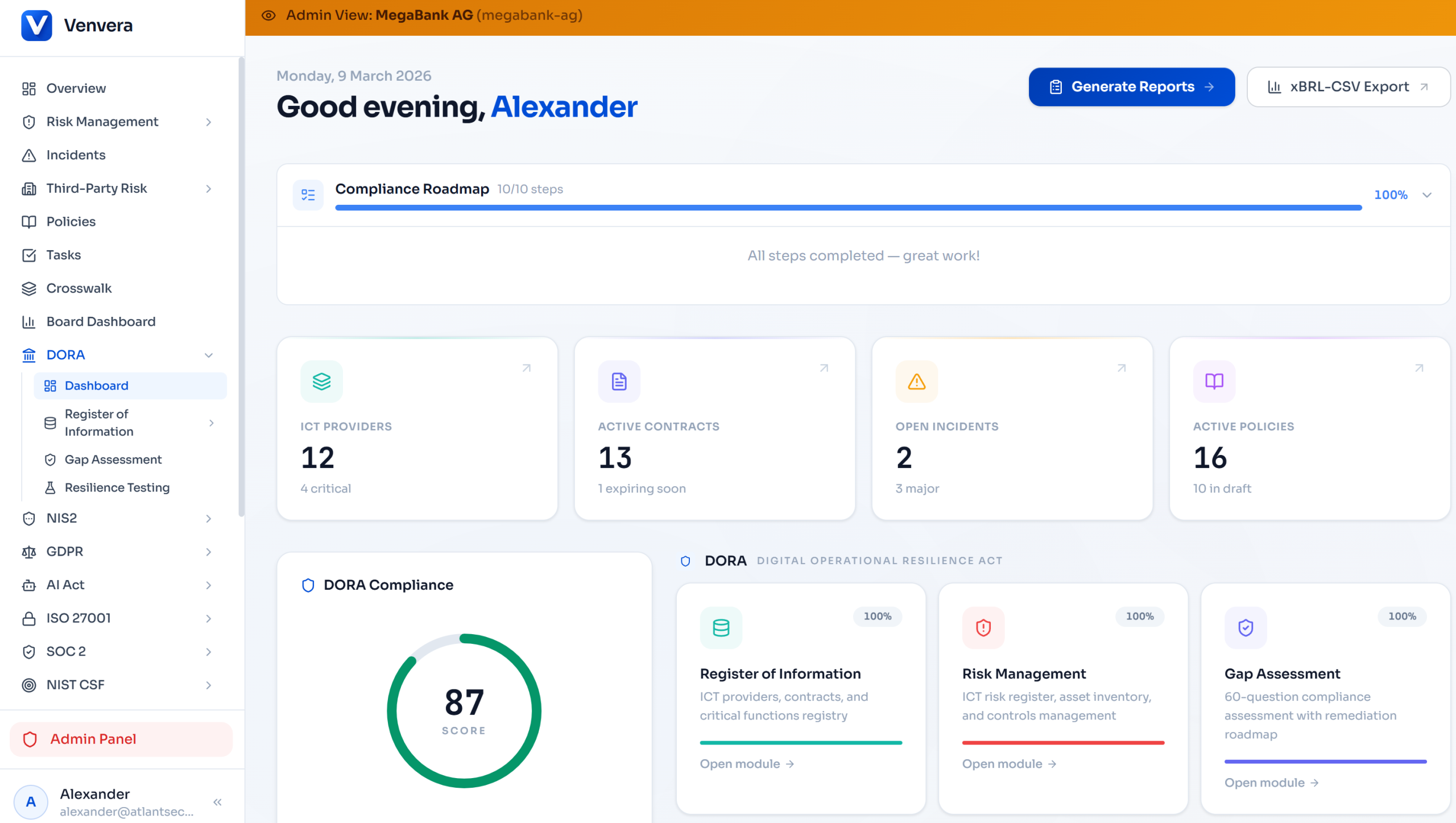
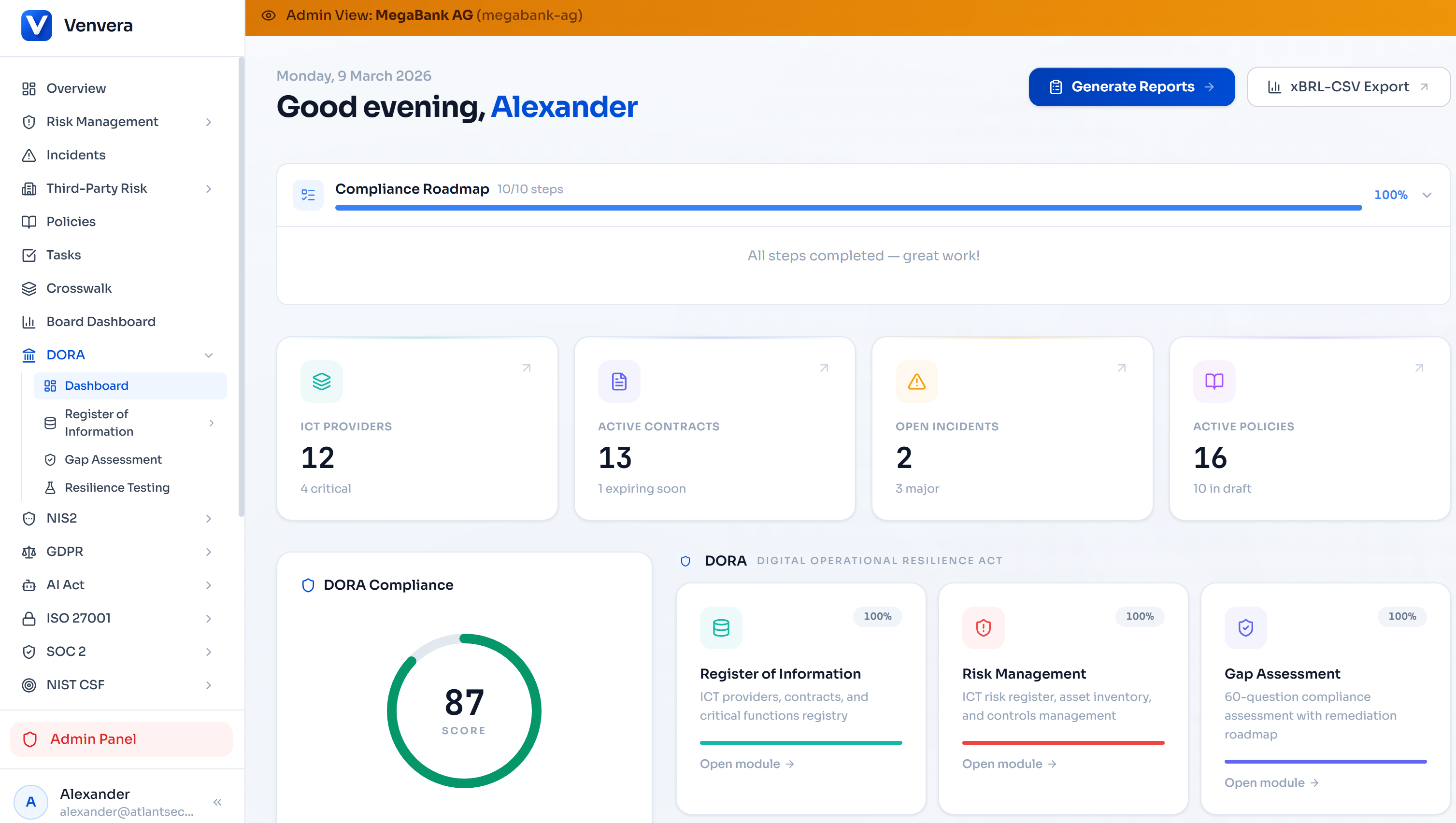
How Venvera Makes You Assessment-Ready
Venvera was purpose-built for this moment. Every feature was designed with the understanding that compliance is about being able to demonstrate it to a supervisor sitting across the table, asking pointed questions, and expecting evidence.
Complete Register of Information
Full RoI module with ICT providers, contractual arrangements, business functions, and sub-outsourcing chains. One-click ESA-format CSV and XBRL export - exactly what your NCA expects. No scrambling to compile spreadsheets.
Gap Assessment with Scores
Built-in gap assessment across all five DORA pillars with article-level scoring. Know exactly where you stand before a supervisor does. Exportable gap reports demonstrate self-awareness and remediation planning.
Board-Ready Reporting
Board-level ICT risk reports satisfying Article 5 requirements. Dashboards showing risk posture, open findings, remediation progress, and incident trends - ready to present to supervisors as evidence of active board engagement.
Evidence Management
Centralized evidence repository with version control, audit trails, and encrypted storage. Retrieve BCP testing results or incident classification matrices in seconds, not days. Every document is timestamped, attributed, and immutable.
Incident Management & Classification
DORA-specific classification with Article 18 severity criteria and built-in NCA reporting timelines (4h/24h/72h). Full incident lifecycle from detection through root cause analysis - demonstrating an operational process, not a theoretical one.
Third-Party Risk & Concentration Analysis
Provider risk assessments, concentration risk dashboards, exit plans, and Art. 30 contract compliance tracking. When a supervisor asks "what if your cloud provider fails?", you have a documented, tested answer.
Audit Trail: Your Secret Weapon
Every action in Venvera is logged in an append-only audit trail - who changed what, when, and why. This is not just a compliance feature; it is a supervisory assessment feature. When an NCA examiner asks "when was this policy last reviewed and by whom?", Venvera provides an irrefutable, timestamped answer. Institutions that can demonstrate this level of traceability consistently receive better assessment outcomes.
DORA enforcement is no longer a future concern. It is happening now. NCAs across Europe are issuing notification letters, dispatching assessment teams, and building the supervisory track records that will define how they engage with your institution for years to come. The first assessments will set precedents - both for what supervisors expect and for how the industry responds.
The question is not whether your institution will be assessed, but when. And when that letter arrives, you want to be reaching for your evidence pack, not starting to build one.
Related Reading
Published March 2026 · Venvera Compliance Platform · venvera.com
This article is for informational purposes and does not constitute legal or regulatory advice. Consult your legal counsel for institution-specific guidance.