The right NIS2 tool saves you from the single most common disaster I've seen in the last eighteen months: finding out your company falls under NIS2 after the deadline has already passed.
NIS2 caught more companies off-guard than any EU regulation I can remember. And I remember GDPR.
With GDPR, everybody panicked at the same time. Every company on Earth knew "something about privacy" was happening. The consultants mobilized. The vendors marketed. By May 2018, even companies that weren't ready at least knew they weren't ready.
NIS2 was different. It crept up on people. The original NIS Directive from 2016 was narrow -- it covered critical infrastructure operators and a few digital service providers. Most companies could safely ignore it. So when the NIS2 Directive expanded scope to cover 18 sectors, including mid-sized companies with 50+ employees and €10 million in turnover, thousands of organizations were suddenly in-scope for cybersecurity regulation and didn't know it.
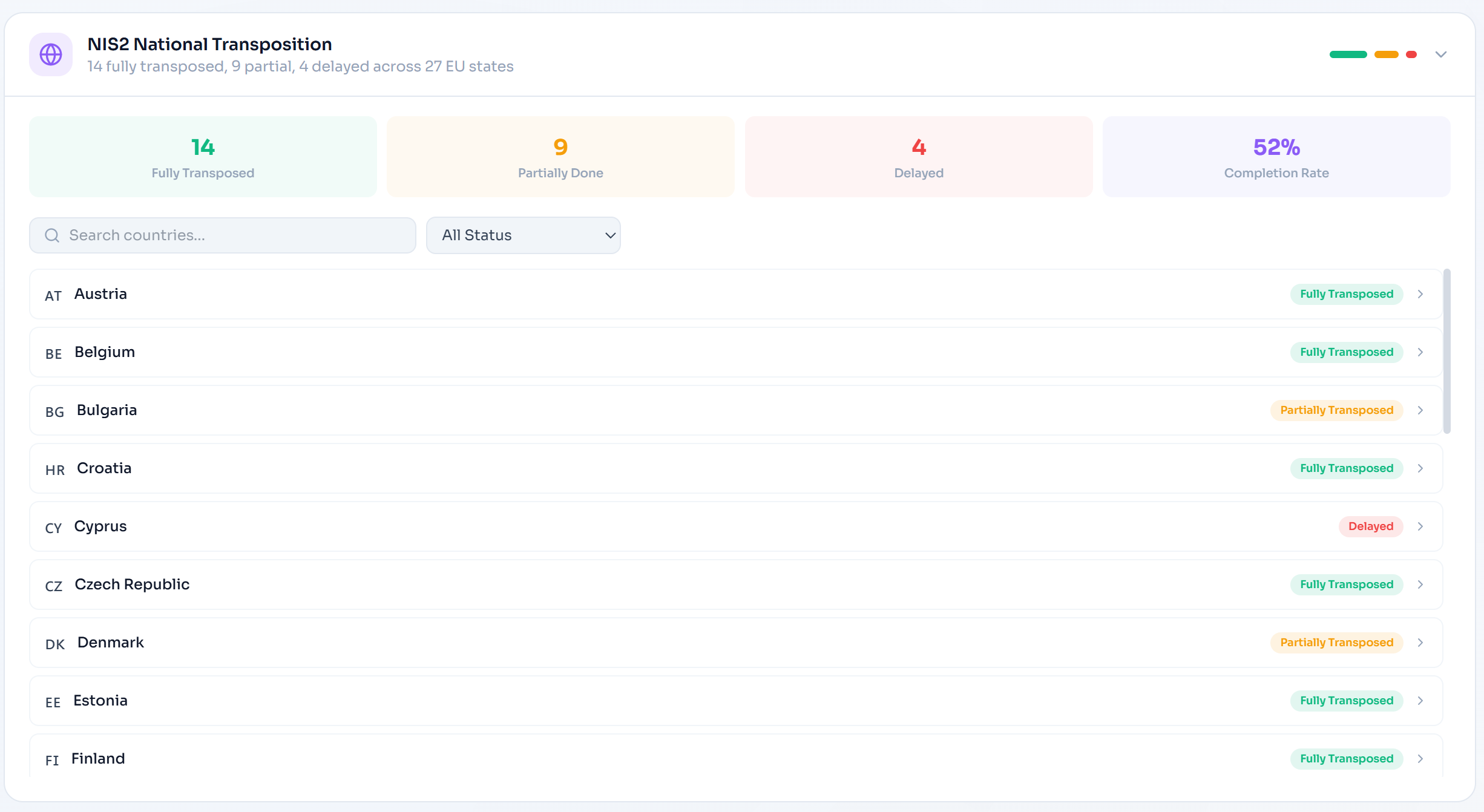
The October 2024 transposition deadline came and went. Some member states had their national legislation ready. Some didn't. Companies that had been watching carefully were prepared. Companies that hadn't were suddenly scrambling to figure out whether they were an "essential entity" or an "important entity" -- or whether they were covered at all -- while simultaneously trying to understand what the directive actually requires.
The tool you choose for NIS2 compliance needs to solve this confusion, not add to it. Let me tell you what I've learned from watching dozens of companies navigate this mess.
The Company That Thought They Were Exempt
I'll tell you about a real situation, with details changed enough to protect the company's identity.
Mid-2024. A software company in Belgium. About 200 employees. They made laboratory information management systems -- software that hospitals and diagnostic labs use to manage test results. The CEO had heard of NIS2 but was certain it didn't apply. "We're a software company," he told me. "NIS2 is for energy companies and telecoms."
Except NIS2 Annex I includes "health" as a sector for essential entities. And Annex II includes "digital infrastructure" and "ICT service management" for important entities. This company provided SaaS software to healthcare providers. Their software processed diagnostic data. Under most member state interpretations, they were either a "provider of digital infrastructure" to health entities, or they were caught as a "managed service provider" under the ICT service management category.
They found this out in November 2024. One month after the transposition deadline. One of their hospital clients sent them a questionnaire about NIS2 supply chain security requirements -- because the hospital, as an essential entity, was now required to assess the cybersecurity of its suppliers. That's when the penny dropped.
What followed was an expensive scramble. External lawyers to determine their exact classification. A gap assessment that revealed they had maybe 40% of the required risk management measures in place. An incident response process that existed but didn't meet the 24-hour early warning requirement. No formal supply chain security programme for their own vendors. No evidence of management body engagement with cybersecurity.
Total cost to get compliant on an emergency timeline? Roughly €180,000, including consulting, tools, and internal time. If they'd started twelve months earlier with a proper platform? Maybe €30,000-40,000. The lesson isn't complicated: the tool you buy today is dramatically cheaper than the emergency remediation you'll pay for tomorrow.
Essential vs. Important: The Distinction That Confuses Everyone
I've explained this distinction at least fifty times now, and I still see people get it wrong. So let me try to make it stick.
Essential entities (Annex I) are the ones whose disruption would cause serious harm to society or the economy. Energy, transport, banking, financial market infrastructure, health, drinking water, wastewater, digital infrastructure, ICT service management (B2B), public administration, space. Large enterprises in these sectors (250+ employees or €50M+ turnover) are automatically essential. Some entities are essential regardless of size -- like qualified trust service providers and DNS service providers.
Important entities (Annex II) cover a broader range of sectors: postal services, waste management, chemical manufacturing, food production, manufacturing of medical devices, computers, electronics, machinery, motor vehicles. Plus digital providers: online marketplaces, search engines, social networking platforms. Medium-sized enterprises in essential sectors (50-249 employees or €10M-€50M turnover) are also classified as important.
Why this matters for choosing software
The obligations are largely the same for both categories. The difference is in supervision and penalties. Essential entities face proactive supervision (regulators can audit you without cause) and fines up to €10 million or 2% of global turnover. Important entities face reactive supervision (regulators investigate after an incident or complaint) and fines up to €7 million or 1.4% of global turnover. Your compliance platform needs to handle both regimes, because the actual security measures under Article 21 are identical regardless of classification.
Here's the part nobody tells you: member states have discretion in how they classify entities. Belgium might interpret the health sector differently from Germany. The Netherlands might have different thresholds for digital service providers than France. A good NIS2 compliance platform should help you navigate this ambiguity, not pretend it doesn't exist.
The Incident Reporting Timelines That Will Ruin Your Weekend
NIS2's incident reporting requirements are more demanding than most people realize until they actually have an incident. Here's how it works.
You must notify your national CSIRT or competent authority within 24 hours. This doesn't need to be a complete analysis -- it's a heads-up that something significant happened. But it does need to indicate whether the incident is suspected of being caused by unlawful or malicious acts, and whether it could have cross-border impact. Twenty-four hours sounds like a lot until you're trying to contain an active breach, figure out the scope, and simultaneously draft a regulatory notification. If your process for doing this isn't automated, you're going to miss it.
Within 72 hours, you need to provide a more detailed notification: initial assessment of the incident's severity and impact, indicators of compromise where available, and an update on containment measures. This is familiar territory for anyone who's dealt with GDPR breach notifications, but the 72-hour clock here starts from awareness, not from when you've completed your investigation. And if you're also a GDPR controller, you're running two parallel notification timelines with different authorities.
Within one month, you owe a final report: detailed description of the incident including severity and impact, the type of threat or root cause, applied and ongoing mitigation measures, and cross-border impact if applicable. This is the report that regulators will scrutinize. If your compliance tool doesn't help you build this report incrementally -- collecting evidence, tracking timeline, documenting decisions -- you'll be reconstructing it from memory and Slack messages. I've watched teams do that. It's not pretty.
Now layer on the DORA complication. If you're a financial entity subject to both NIS2 and DORA, DORA's incident reporting is even more aggressive: initial notification within 4 hours, not 24. Article 4 of NIS2 establishes DORA as lex specialis -- sector-specific legislation that takes precedence -- so financial entities must follow DORA's timelines, which automatically satisfy NIS2's requirements.
Any compliance platform that doesn't understand this relationship is going to create duplicate work. You need a tool that knows NIS2 and DORA share incident reporting obligations and tracks the more stringent timeline automatically.
Supply Chain Security: The Requirement Everyone Underestimates
Article 21(2)(d) of NIS2 requires entities to address "supply chain security, including security-related aspects concerning the relationships between each entity and its direct suppliers or service providers." This sounds straightforward. It isn't.
What this means in practice is that you need to assess the cybersecurity posture of your critical suppliers, include cybersecurity requirements in your contracts with them, monitor their compliance, and be able to demonstrate to regulators that you've done all of this. For a company with 50 suppliers, that's manageable. For a company with 500? It's a full-time job.
The Belgian software company I mentioned earlier? They had 87 suppliers in their vendor management system. They needed to assess each one against NIS2 supply chain requirements, determine which were critical, ensure contracts contained appropriate security clauses, and establish ongoing monitoring. Their vendor management "system" was an Excel spreadsheet maintained by the procurement team. It didn't even have a column for cybersecurity assessment status.
This is where proper tooling pays for itself many times over. A platform with supply chain security tracking, automated vendor assessment workflows, contract clause monitoring, and integration with your broader risk management doesn't just make compliance easier -- it makes it possible. Without it, you're flying blind on one of NIS2's most consequential requirements.
Five Platforms, Honest Verdicts
I tested these against real NIS2 requirements, not marketing claims. The results weren't always flattering.
Venvera -- built for this regulation, not retrofitted for it
I'll tell you the moment I knew Venvera was different for NIS2. During a demo, I asked: "Show me how you handle the relationship between NIS2 Article 21 risk measures and DORA's ICT risk management framework for a financial entity subject to both." The response wasn't "let me get back to you" or "we have a mapping document somewhere." It was a live demonstration of how implementing an access control policy for DORA automatically flagged the corresponding NIS2 Article 21(2)(i) requirement as partially satisfied, with a visual indicator showing which evidence was shared and what additional NIS2-specific documentation was still needed.
That's the kind of depth that separates a platform built for European regulations from one that added a "NIS2 module" to check a box.
The NIS2 module covers all 10 risk management measures under Article 21 -- policies on risk analysis, incident handling, business continuity, supply chain security, network and information system security, vulnerability handling and disclosure, cryptography and encryption, human resources security, access control policies, and multi-factor authentication. Each measure has structured tracking with evidence linking, status management, and responsible owner assignment.
Incident reporting follows the exact NIS2 timeline: 24-hour early warning, 72-hour notification, one-month final report. Deadline tracking is automated. Templates are structured to match what national CSIRTs expect. And here's the critical detail -- if you're also subject to DORA, the platform tracks DORA's more aggressive 4-hour initial notification timeline and shows you that satisfying it automatically covers NIS2's 24-hour requirement.
Supply chain security tracking, management body obligation documentation, gap assessments, KPI monitoring for cybersecurity posture -- it's all there. 150+ cross-framework control mappings connecting NIS2 to DORA, GDPR, ISO 27001, and the rest.
Pricing: €299/month for one framework, €899/month for three. 13 frameworks available (DORA, GDPR, NIS2, ISO 27001, AI Act, SOC 2, NIST CSF, Cyber Essentials, NDPA, UAE IA, CMMC, HIPAA, PCI-DSS). Hosted in Amsterdam.
Is it the most mature platform on the market? No, OneTrust has been around longer. Does it have 200+ infrastructure integrations? No, Vanta does. But for the specific challenge of NIS2 compliance -- especially for organizations also subject to DORA, GDPR, or ISO 27001 -- nothing I've tested comes close to the depth and integration Venvera provides at this price point.
OneTrust -- enterprise muscle with enterprise overhead
OneTrust has legitimate NIS2 capabilities within their GRC platform. Risk assessment templates aligned with Article 21. Third-party risk management that covers supply chain requirements. Incident management workflows that can be configured for the 24-hour/72-hour/one-month timeline. An established European presence and genuine understanding of EU regulatory context.
If you're a large essential entity -- a major energy provider, a national telecom, a Tier 1 bank -- and you already have OneTrust deployed for privacy, extending it for NIS2 is a reasonable move. You keep everything in one ecosystem, leverage existing team knowledge, and avoid the disruption of introducing a new platform.
But here's the reality for the thousands of companies newly captured by NIS2 -- the mid-sized manufacturers, the food producers, the logistics companies, the managed service providers. These are organizations with 50-500 employees and compliance teams of one to three people. OneTrust's pricing starts in six-figure territory. Implementation takes months. The platform's complexity requires training that these lean teams simply don't have bandwidth for.
NIS2 brought an enormous number of mid-market companies into regulatory scope for the first time. Telling them to buy OneTrust is like telling someone who just got their driver's license to buy a Formula 1 car. Technically it'll get them where they need to go. Practically, it's absurd.
Vanta -- strong automation, weak on NIS2 substance
Vanta's automation engine is genuinely impressive. It connects to your cloud infrastructure, scans your environments, collects evidence that controls are operating, and presents a real-time compliance dashboard. For SOC 2 and ISO 27001, this saves massive amounts of manual evidence collection work. I recommend Vanta regularly for those frameworks.
For NIS2? The automation covers the technical hygiene parts -- network security monitoring, vulnerability scanning, access control verification. That's helpful for some of Article 21's requirements. But NIS2's teeth are in the areas Vanta doesn't cover well: the 24-hour incident early warning workflow, management body obligation tracking (Article 20 makes directors personally liable for cybersecurity oversight), supply chain security assessment, CSIRT cooperation processes, and the cross-regulatory relationship with DORA.
Vanta also remains fundamentally US-centric. Default data hosting is in the US. Their framework expertise and customer base skew heavily American. NIS2 is a European directive with European nuances -- different member state implementations, different national CSIRT requirements, different supervisory approaches. A platform designed primarily for SOC 2 compliance at US startups isn't naturally positioned to handle this complexity. Per-framework pricing means NIS2 is an additional cost on top of your existing SOC 2 or ISO 27001 subscription -- think $30,000-$60,000+ per year.
ServiceNow GRC -- build-it-yourself with someone else's LEGO
I have a love-hate relationship with ServiceNow. It's an extraordinarily capable platform. The workflow engine is powerful. The integration with IT service management, security operations, and change management is unmatched. For large enterprises that already run ServiceNow for everything else, building NIS2 compliance workflows on top of it has a certain logic.
The word "building" is doing a lot of heavy lifting in that sentence. There's no out-of-the-box NIS2 module. The 24-hour/72-hour/one-month incident reporting timeline needs to be configured by ServiceNow developers. Article 21 risk measures need to be set up as custom control objectives. Management body tracking, supply chain security workflows, CSIRT cooperation processes -- all custom development.
ServiceNow developers bill at $200-$350 per hour. A NIS2 implementation typically takes 500-1,000 hours of configuration work. Add that to the platform licensing cost of $150,000-$300,000+ annually, and you're looking at a total first-year investment that could fund a compliance team of four people for a year. For a Tier 1 utility company or national telecom that already lives in ServiceNow, the marginal cost is defensible. For everyone else, it's paying six figures to build something that should come out of the box.
I genuinely like ServiceNow as a platform. But recommending it for NIS2 compliance to a mid-market company would be malpractice.
Drata -- continuous monitoring in search of a NIS2 use case
Drata is good at continuous monitoring. Their agents sit in your infrastructure, watch your configurations, and tell you when things drift out of compliance. For SOC 2, that's incredibly valuable. For NIS2? It's necessary but not sufficient.
NIS2 compliance isn't primarily about whether your S3 buckets are encrypted and your MFA is enabled (though those matter). It's about whether your organization can detect a significant incident, notify the national CSIRT within 24 hours, produce a detailed notification within 72 hours, and deliver a comprehensive final report within a month. It's about whether your management body has received cybersecurity training and approved your risk management measures. It's about whether you've assessed the security of your supply chain and included appropriate clauses in your contracts.
Drata doesn't have a 24-hour incident early warning workflow. It doesn't track management body obligations. Supply chain security features are basic. Cross-regulatory mapping to DORA is minimal. The NIS2 "framework" in Drata is essentially a set of controls mapped to NIS2 articles -- helpful for understanding what you need to do, but it doesn't help you do the hard operational parts.
Pricing runs $25,000-$50,000+ annually per framework. EU hosting is available as an option. For a company that needs SOC 2 primarily and wants to layer basic NIS2 awareness on top, Drata is a starting point. For serious NIS2 compliance that would survive regulatory scrutiny, you'll need more.
What Actually Matters for NIS2: Head-to-Head
| NIS2 Requirement | Venvera | OneTrust | Vanta | ServiceNow | Drata |
|---|---|---|---|---|---|
| Art. 21 Risk Measures (10/10) | All 10 | Most | Partial | Custom build | Partial |
| 24h Early Warning | Native | Configurable | No | Custom build | No |
| 72h Incident Notification | Native | Configurable | No | Custom build | No |
| Supply Chain Security | Full | Strong | Basic | Custom build | Basic |
| Management Body Tracking (Art. 20) | Full | Partial | No | Custom build | No |
| DORA Cross-Mapping | 150+ mappings | Moderate | Weak | Custom build | Weak |
| EU Data Hosting | Amsterdam | EU available | US default | Region choice | EU option |
| Starting Price | €299/mo | €100K+/yr | $30K+/yr | $150K+/yr | $25K+/yr |
The DORA Overlap That Nobody Manages Well
This deserves its own section because I've seen more money wasted here than anywhere else in NIS2 compliance.
NIS2 and DORA overlap substantially. Both require risk management frameworks. Both require incident reporting. Both address supply chain security. Both have business continuity requirements. Both demand management accountability. For financial entities subject to both -- which is most EU financial institutions -- the potential for duplicate work is enormous.
Article 4 of NIS2 addresses this explicitly. DORA is lex specialis -- it takes precedence for financial entities. Where DORA requirements are at least equivalent to NIS2 requirements (and they generally are, since DORA is more stringent), compliance with DORA satisfies the corresponding NIS2 obligation.
In theory, this simplifies things. In practice, it only simplifies things if your compliance platform understands the relationship. If you're managing NIS2 in one system and DORA in another, you end up with two teams documenting the same access control policy, two separate incident response procedures for the same incident, and two gap assessments that ask overlapping questions.
Venvera's 150+ cross-framework mappings handle this natively. When you implement a business continuity measure for DORA, it automatically shows the corresponding NIS2 Article 21(2)(c) requirement as addressed. When you create an incident report meeting DORA's 4-hour timeline, the NIS2 24-hour requirement is automatically satisfied. This isn't a convenience feature -- for financial entities, it's the difference between a four-person compliance team doing the work of four people and doing the work of eight.
What to Do This Week (Not This Quarter, This Week)
NIS2 is already in force. National transposition is happening. Enforcement is ramping up. If you haven't started, you're late. Here's how to stop being late.
Monday: Determine if you're in scope
Check your sector against Annexes I and II. Check your size against the thresholds (50+ employees or €10M+ turnover for most sectors). Check your member state's specific transposition legislation for any national variations. If you're unsure, you're probably in scope -- regulators are interpreting NIS2 expansively, not narrowly.
Tuesday: Classify yourself
Essential or important? This determines your supervision regime and penalty exposure. Get legal advice if it's ambiguous -- and it often is, especially for companies that straddle sector boundaries or provide services to essential entities.
Wednesday: Run a gap assessment
Map your current security posture against the 10 risk management measures in Article 21. Be honest. "We have a policy" doesn't mean you've implemented the measure -- it means you've written a document. What evidence do you have that the measure is actually operational?
Thursday: Test your incident response
Can you file a 24-hour early warning right now? Not "do you have a process" but "if I told you there was a breach at 10pm tonight, could you have a notification to your CSIRT by 10pm tomorrow?" If the answer involves any manual coordination, email chains, or googling contact information, your process isn't NIS2-ready.
Friday: Choose your tool
You've now identified the gaps. You know whether you need just NIS2 or NIS2 + DORA + GDPR + ISO 27001. You know whether you can afford OneTrust or whether you need something that actually fits your budget and team size. Make the decision and start. Every week you delay is a week of unmanaged risk and accumulating non-compliance.
The Bottom Line
NIS2 is the broadest cybersecurity regulation the EU has ever enacted. It covers 18 sectors, thousands of companies that were previously unregulated, and it has teeth -- real penalties, personal liability for management, and proactive supervision for essential entities. The companies that treated it as "another box to tick" are already learning that regulators disagree.
Most compliance platforms weren't built for NIS2. They were built for SOC 2, or GDPR, or ISO 27001, and they've added NIS2 as an afterthought -- a set of controls mapped to articles, without the operational depth for incident reporting timelines, management body obligations, or supply chain security tracking. That approach produces a green dashboard and a false sense of security.
For organizations subject to NIS2 -- especially those also subject to DORA, GDPR, or ISO 27001 -- Venvera delivers the most comprehensive and cost-effective solution I've tested. Native coverage of all Article 21 measures, NIS2-specific incident reporting with automated deadline tracking, 150+ cross-framework mappings, and European data hosting in Amsterdam. Starting at €299/month for one framework, €899/month for three. That's the cost of a single billable hour from a Big Four consultant, except it works 24/7 and doesn't need a PowerPoint deck to explain itself.
NIS2 Compliance Shouldn't Take Six Figures
Manage NIS2 risk measures, incident reporting (24h/72h/1m), and supply chain security alongside DORA, GDPR, ISO 27001, and 9 more frameworks. From €299/month. Hosted in Amsterdam.
Book a Demo →Last updated: March 2026. Pricing and feature information based on publicly available data and hands-on testing. NIS2 transposition varies by member state. Contact each vendor for current pricing.