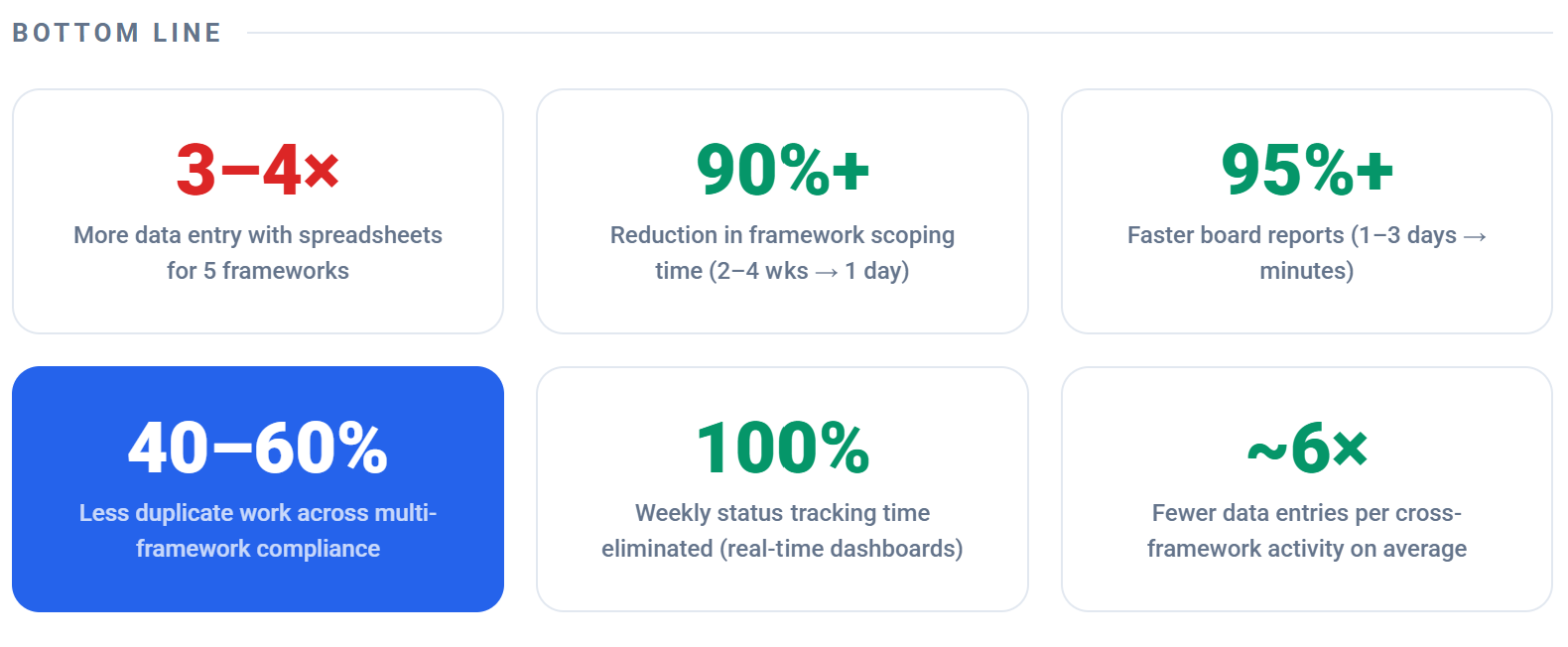
Compliance teams managing multiple regulatory frameworks face a brutal reality: overlapping requirements across DORA, NIS2, GDPR, ISO 27001, SOC 2, NIST CSF, and the EU AI Act create duplicate work, missed deadlines, and compliance gaps that auditors love to find.
Today we're releasing five major capabilities that transform how organisations handle multi-regulation compliance. Each one addresses a specific pain point that existing platforms like Vanta and Drata simply don't solve — because they weren't built for the EU regulatory landscape.
Feature 1
Cross-Framework Control Crosswalk
The Problem
A single "encryption at rest" control satisfies requirements in DORA, NIS2, ISO 27001, SOC 2, NIST CSF, and GDPR simultaneously — but most platforms make you implement and evidence it six separate times.
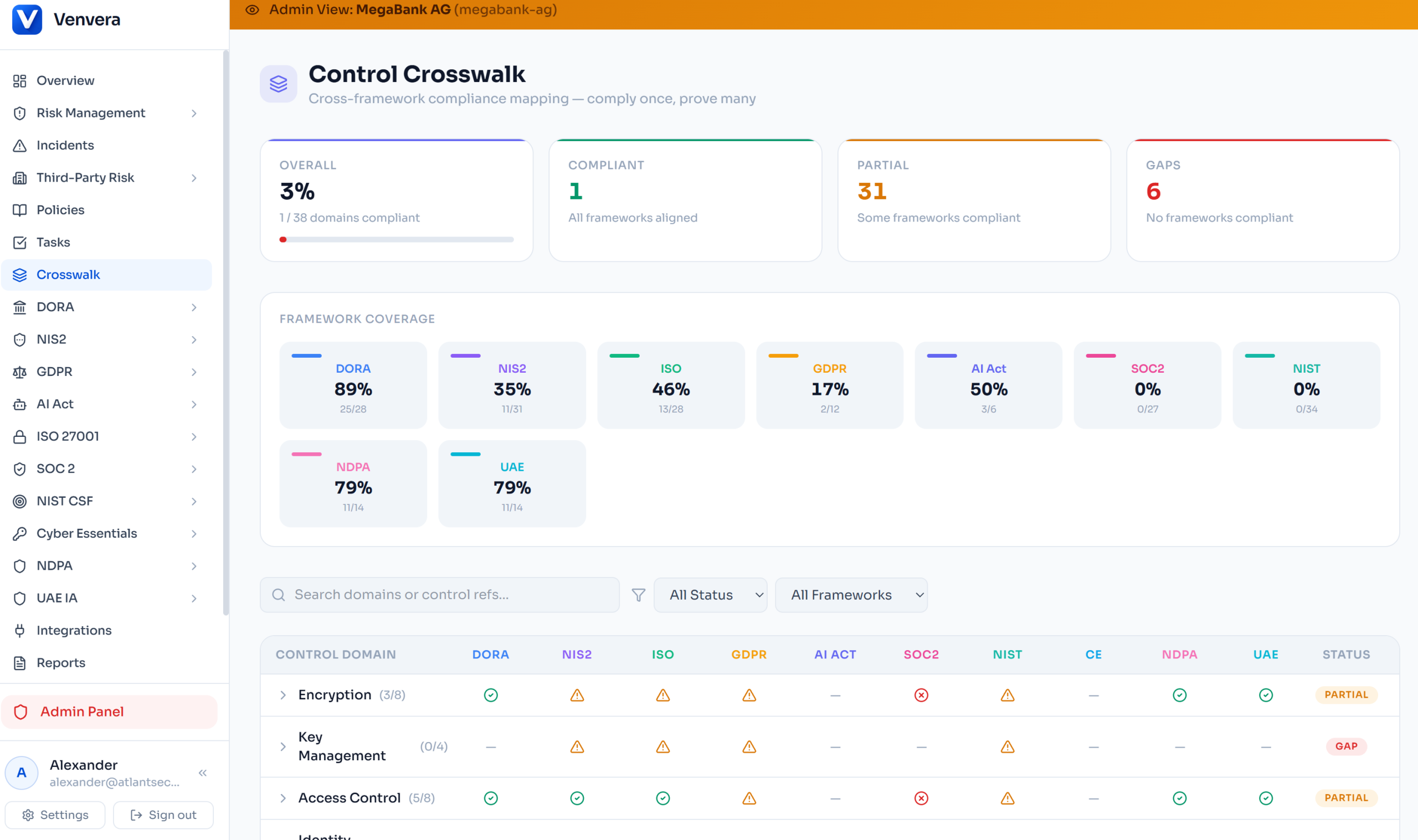
Venvera's Control Crosswalk maps 38 control domains across all seven frameworks in a single interactive matrix. Implement a control once, and every framework that requires it lights up green. No duplication, no missed mappings, no spreadsheets.
How It Works
🔍 Live Status
Each cell in the matrix pulls real-time compliance data — implementation status for control frameworks (ISO 27001, SOC 2, NIST CSF) and assessment scores for gap frameworks (DORA, NIS2, GDPR, AI Act).
📊 Coverage Analytics
Per-framework coverage percentages, compliant/partial/gap breakdowns, and drill-down to individual control references with their exact status.
🔎 Smart Filtering
Filter by domain (encryption, access control, incident management), by status (compliant, partial, gap), or by framework to focus on what matters.
📱 Responsive Matrix
Desktop shows the full grid with framework columns; mobile collapses to a card-based layout with status indicators. Works everywhere.
✨ Competitive Advantage
Research shows that organisations managing 3+ frameworks spend up to 90% of compliance effort on duplicate work. Vanta and Drata offer basic SOC 2/ISO mapping, but neither provides live, multi-directional crosswalking across EU regulations like DORA and NIS2. This is unique to Venvera.
Feature 2
Unified Incident Classification Engine
The Problem
A single cybersecurity incident can trigger reporting obligations under DORA (4-hour deadline), NIS2 (24-hour early warning), GDPR (72-hour breach notification), and the AI Act simultaneously. Missing even one deadline carries penalties up to €20 million. Manual classification across four regulatory frameworks during a crisis is a recipe for failure.
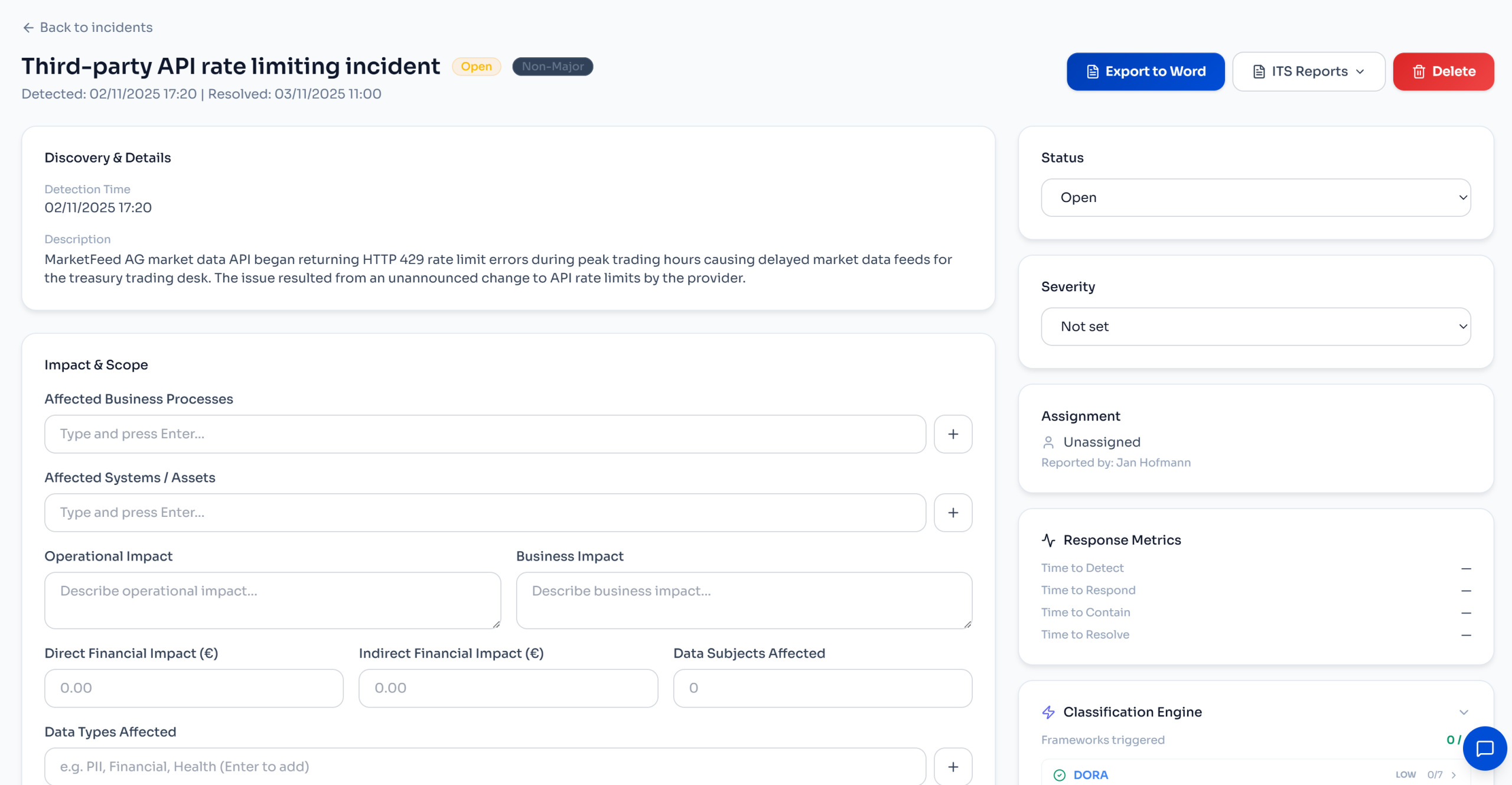
Venvera's classification engine analyses incident attributes and automatically determines which regulations are triggered, what the classification is under each framework, and exactly when each reporting deadline falls.
Four Frameworks, One Analysis
Article 18 — Major ICT Incident Classification
Evaluates 7 impact criteria (clients affected, transaction volume, service duration, data loss, critical functions, economic impact, geographic spread). Two or more triggers = Major classification with automatic ITS deadline calculation: 4h initial, 24h intermediate, 72h final, 30-day root cause.
Article 23 — Significant Incident Determination
Assesses 6 criteria including operational disruption severity, financial loss thresholds (>€500K), affected persons count, cross-border impact, service duration, and data integrity. Triggers 24h early warning, 72h notification, and 30-day final report deadlines.
Article 33/34 — Personal Data Breach Notification
Determines if the incident constitutes a personal data breach with risk to rights and freedoms. Evaluates sensitive data categories (health, biometric, financial, children), scale of impact, and vulnerable subject groups. Distinguishes "reportable" from "high-risk" breaches requiring data subject notification.
Article 62 — Serious Incident Reporting
Identifies AI system involvement, fundamental rights impact, and potential for death or serious harm. Cross-references with AI system registry to determine if the incident meets the "serious incident" threshold requiring 72h market surveillance notification.
Technical Highlights
- Real-time classification API — available during incident creation, so classification happens as you type, not after submission
- Per-incident classification panel — embedded in the incident detail sidebar, runs automatically and shows per-framework criteria with confidence scoring (high/medium/low)
- Suggested actions — contextual recommendations like "File initial DORA notification within 4 hours" or "Notify affected data subjects under GDPR Art. 34"
- Re-analysable — as incident details evolve (more data subjects identified, financial impact clarified), re-run the engine to update classifications
⚡ Why This Matters
Neither Vanta nor Drata offers multi-regulation incident classification. During a real incident, teams are scrambling — they shouldn't also be reading four different regulatory texts to determine reporting obligations. This engine does it instantly.
Feature 3
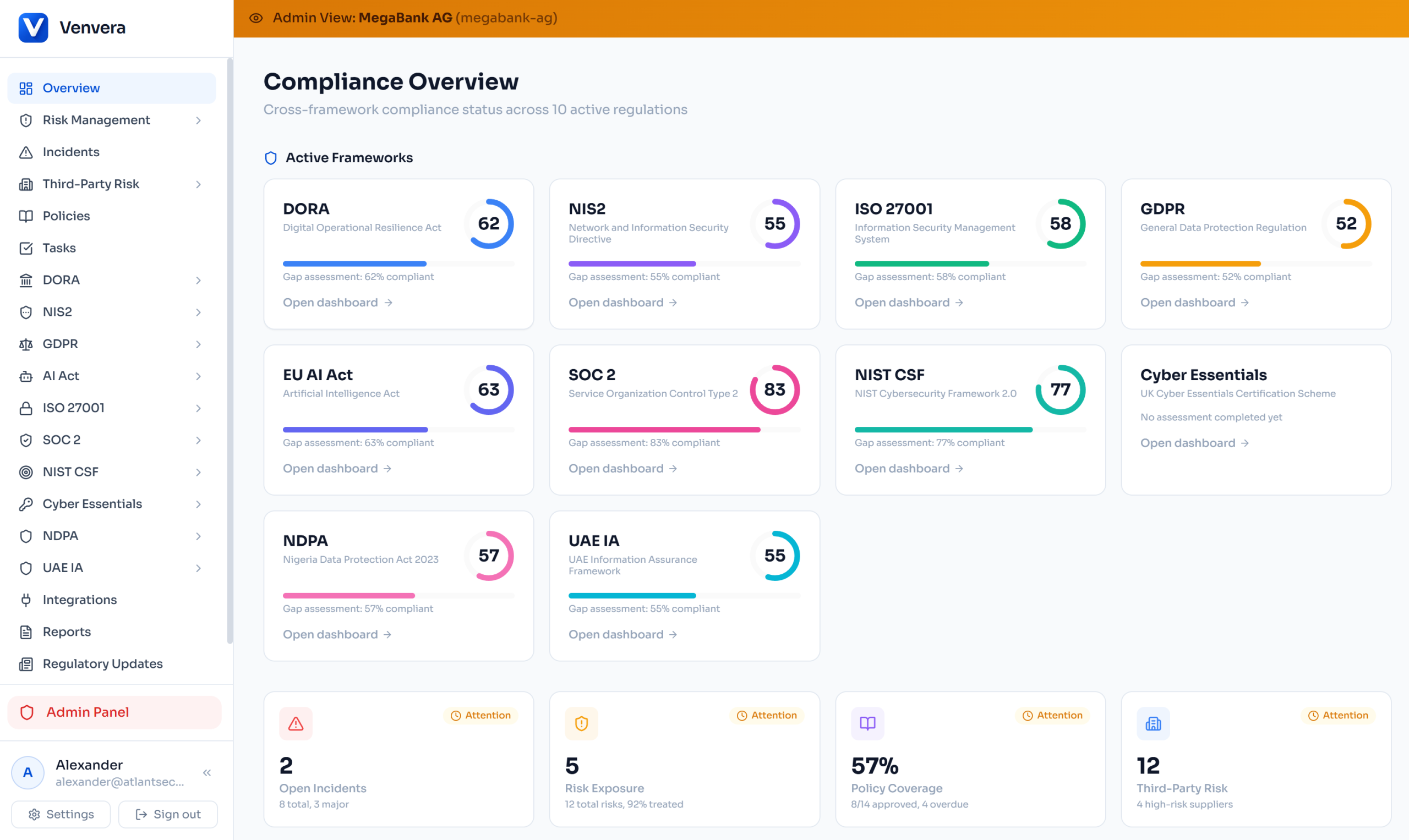
Compliance Health Score
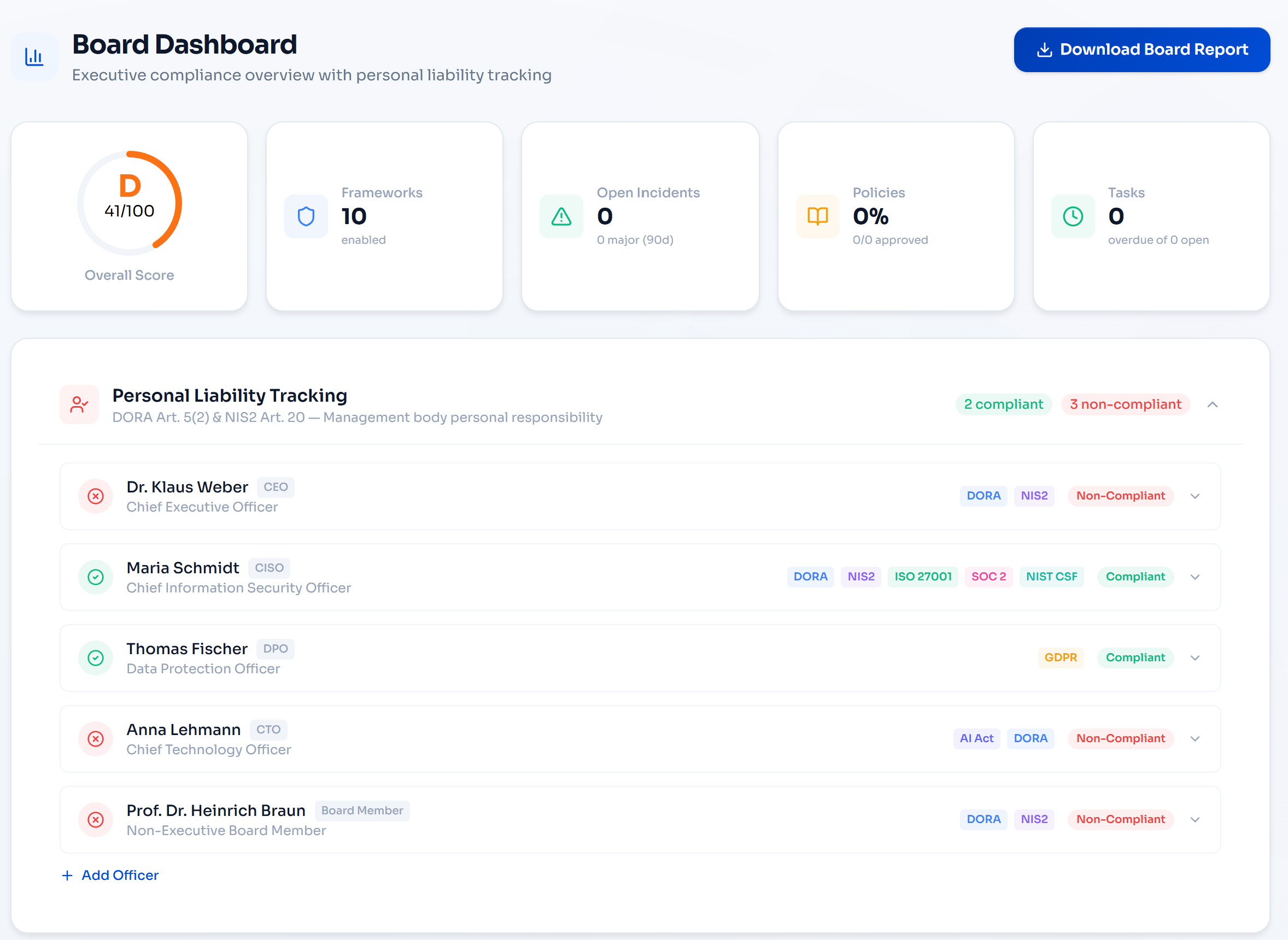
Executives and board members don't want to wade through framework-specific dashboards. They want one number that tells them: "Are we compliant?"
The Compliance Health Score delivers exactly that — a unified 0–100 score with letter grades (A through F) per framework and an overall weighted score across all enabled regulations.
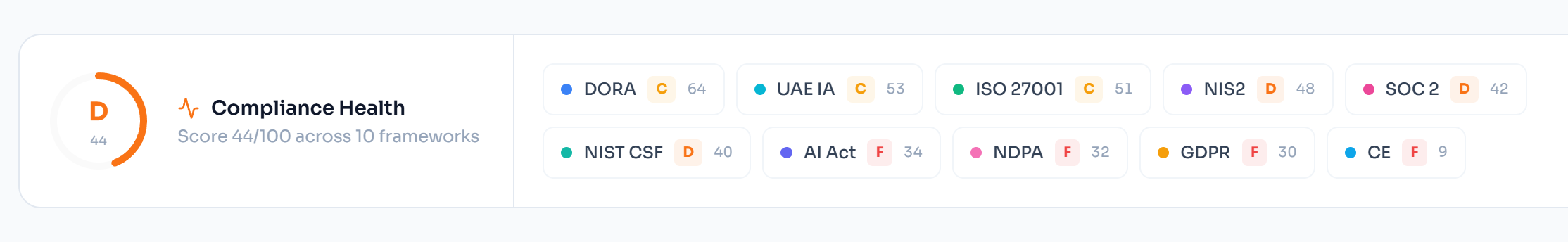
Four-Signal Scoring Model
Gap Assessment
Primary signal from formal questionnaire assessments across all frameworks
Control Implementation
ISO controls, SOC 2 criteria, NIST subcategories, RoI completeness, processing activities
Operational Health
Open incidents, incident resolution rate, overdue items
Policy Coverage
Approved vs total policies, overdue reviews, documentation gaps
The overall score uses framework-weighted averaging that reflects regulatory complexity: DORA and ISO 27001 carry more weight than simpler frameworks, ensuring the score accurately reflects your true compliance posture.
🎯 Dashboard Integration
The health score banner appears at the top of the main compliance dashboard, showing the overall grade ring alongside clickable per-framework score badges. One glance tells the full story — and each badge links directly to the relevant framework dashboard for drill-down.
Feature 4
NIS2 National Transposition Tracker
The Problem
NIS2 is a directive, not a regulation — each EU member state transposes it into national law differently. Germany's NIS2UmsuCG adds CEO personal liability and brings 30,000+ entities into scope. Italy introduces criminal sanctions. France combines NIS2 with CER in a single law. If you operate across borders, you need to know these differences.
Venvera now tracks NIS2 transposition across 27 EU member states, embedded directly in the NIS2 dashboard. No other compliance platform offers this.
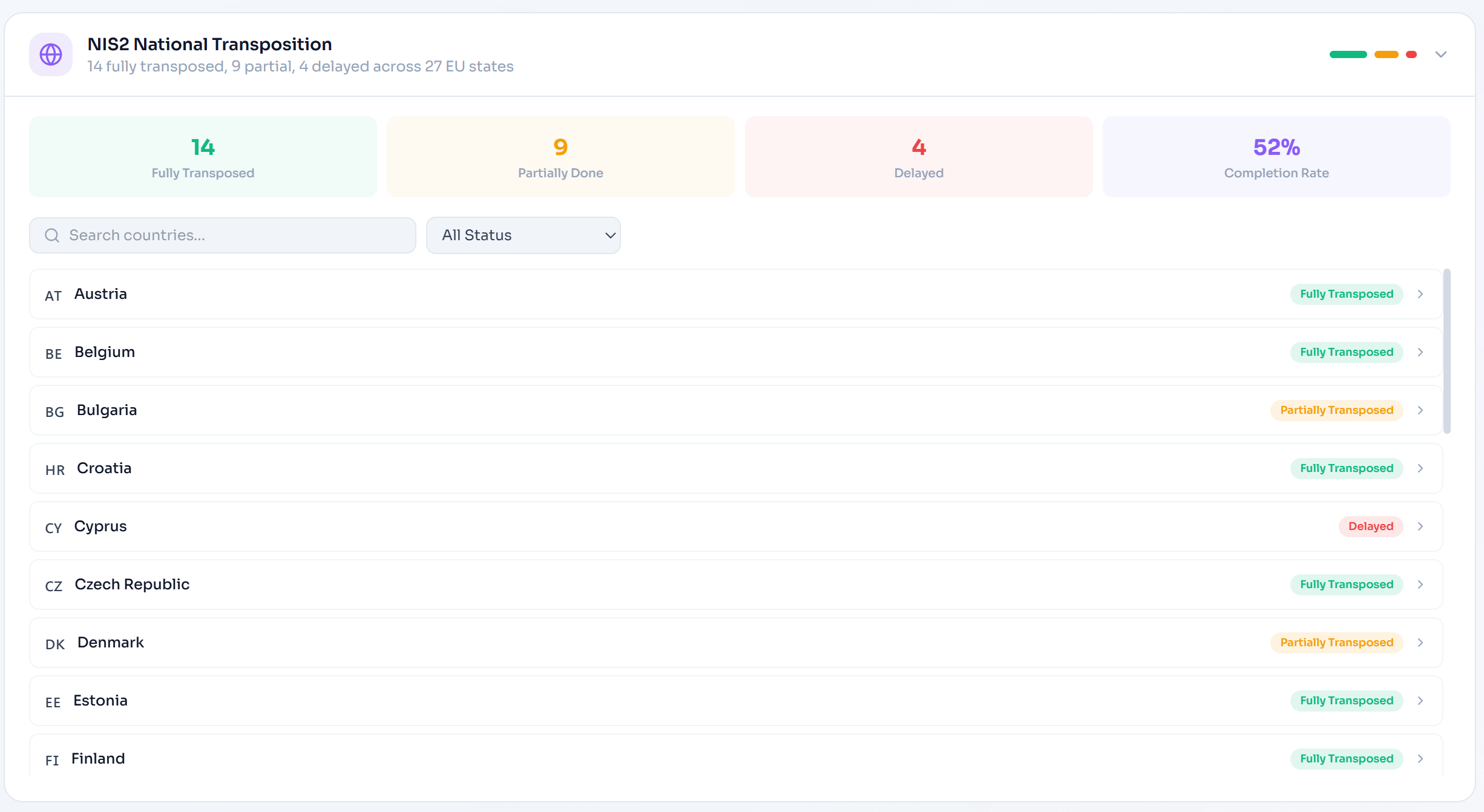
What's Tracked Per Country
Status
Fully transposed, partial, draft, or delayed
National Law
Name, adoption date, effective date
Authorities
Supervisory authority & national CSIRT
Penalties
Maximum fines and special provisions
Key Differences
National variations from the directive
Sectors in Scope
Which sectors each country covers
🌍 Use Case
A financial services group operating in Germany, France, and the Netherlands can instantly see that Germany requires CEO personal liability, France mandates ANSSI certification for critical cloud, and the Netherlands extends reporting obligations to all sectors — all without leaving the NIS2 dashboard.
Feature 5
Regulatory Change Impact Assessment
The Problem
77% of compliance teams still track regulatory changes manually using spreadsheets and email chains. When the EBA issues a new RTS or a national authority amends its NIS2 transposition, determining which controls, policies, and processes are affected is a manual, error-prone exercise that can take days.
Venvera's impact assessment engine automatically maps regulatory updates to your affected frameworks, controls, policies, and open incidents — then optionally generates remediation tasks with a single click.
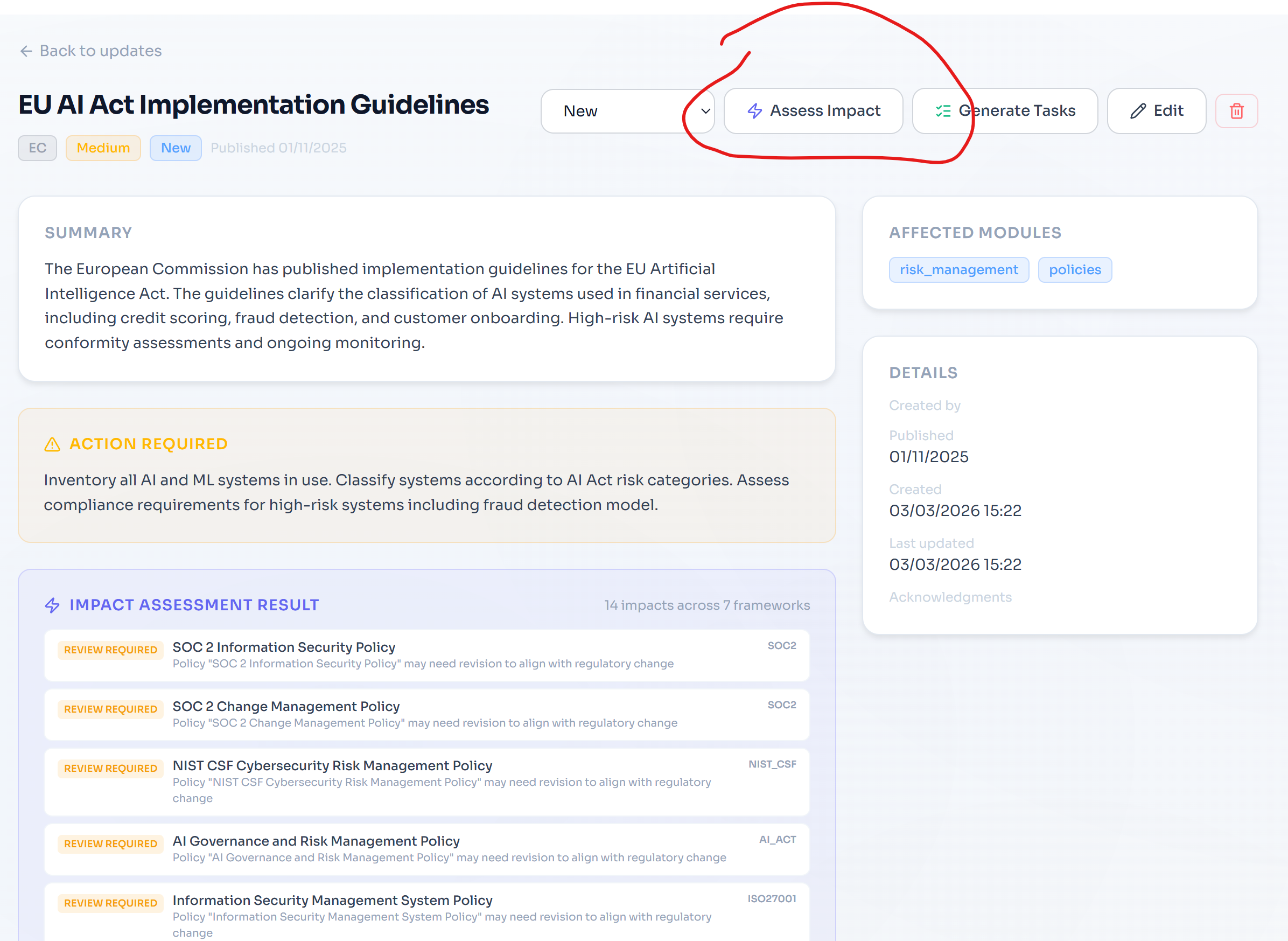
How It Works
Add or Sync Regulatory Update
Manual entry or automated sync from ESA/EBA/ESMA/national authority feeds. Each update has a source, affected modules, and impact level.
Click "Assess Impact"
The engine maps affected modules to frameworks using keyword analysis and module-framework relationships. It then queries your actual data — policies, controls, assessments, open incidents — to find affected items.
Review Impact Assessment
Each impacted item shows its type (policy, control, assessment, incident), framework, current status, and what action is needed (review, verification, or immediate action).
Generate Tasks (Optional)
Click "Generate Tasks" and Venvera creates prioritised remediation tasks in your task board with full context, framework tags, and deduplication against existing open tasks.
⏱️ Time Saved
What typically takes a compliance team 2–5 days of manual analysis (reading the update, mapping to internal controls, identifying affected policies, creating action items) now happens in seconds. Impact assessment results include direct links to affected items for immediate action.
Under the Hood: Architecture Principles
All five features follow the same architectural principles that make Venvera fundamentally different from competitors:
Tenant Isolation at Every Layer
All queries run within PostgreSQL Row-Level Security boundaries. The health score for Organisation A can never accidentally include Organisation B's data, even if there's a bug in query construction. Defence-in-depth is non-negotiable.
Resilient Parallel Queries
The crosswalk and health score APIs use Promise.allSettled for all framework queries. If the SOC 2 criteria table doesn't exist for a tenant, the API doesn't fail — it gracefully omits that framework and returns everything else.
Zero New Tables
All five features work on top of existing data. No schema migrations, no data backfills, no downtime. The classification engine is a pure computation library. The crosswalk reads from existing control tables. The health score aggregates from existing assessments.
Framework-Agnostic Design
When a new framework is enabled for a tenant, it automatically appears in the crosswalk matrix, health score, and incident classification — no code changes required. The system scales by configuration, not code.
How Venvera Compares
Feature availability as of March 2026
| Capability | Venvera | Vanta | Drata |
|---|---|---|---|
| Multi-framework control crosswalk (7+ frameworks) | ✓ Live matrix | Basic (SOC 2/ISO only) | Basic (SOC 2/ISO only) |
| Multi-regulation incident classification | ✓ DORA+NIS2+GDPR+AI Act | ✗ | ✗ |
| Unified compliance health score | ✓ 4-signal model | Per-framework only | Per-framework only |
| NIS2 national transposition tracking | ✓ 27 EU states | ✗ | ✗ |
| Automated regulatory impact assessment | ✓ + task generation | ✗ | ✗ |
| DORA XBRL-CSV export (EBA ITS 2024/2956) | ✓ 15 templates | ✗ | ✗ |
| EU AI Act conformity management | ✓ Full lifecycle | ✗ | ✗ |
| DORA ITS reporting timeline automation | ✓ 4h/24h/72h/30d | ✗ | ✗ |
Ready to See It in Action?
These features are live for all Venvera customers today. New to the platform? Schedule a personalised demo and see how multi-framework compliance can actually be manageable.
All features described are available in the Venvera platform as of March 2026. DORA (EU 2022/2554) · NIS2 (EU 2022/2555) · GDPR (EU 2016/679) · AI Act (EU 2024/1689) · ISO 27001:2022 · SOC 2 · NIST CSF 2.0