If you're evaluating compliance platforms in 2026, you've probably come across Vanta. It's well-known, well-funded, and dominates SOC 2 automation for US tech companies. But here's the uncomfortable truth: Vanta was built for American startups chasing SOC 2 badges, not for European financial institutions navigating DORA, NIS2, GDPR, and the EU AI Act simultaneously.
We built Venvera because we lived the pain. We watched compliance teams at EU financial entities try to force-fit American compliance tools into European regulatory realities — and fail. Expensive subscriptions, bolted-on framework support, manual workarounds for requirements Vanta simply doesn't understand. This is a detailed, honest breakdown of where Vanta falls short and why Venvera exists.
Comparison 1
Pricing: Transparent vs. “Call Us”
The Pain
Vanta's pricing is opaque by design. You won't find a price on their website — just a "Contact Sales" button. Once you get through the demo calls, the reality hits: $10,000–$15,000/year for a single framework, with each additional framework adding ~$5,000/year. For EU financial institutions needing 5+ frameworks, costs quickly spiral to $30,000–$50,000+ annually — before external audits, pen testing, and add-on fees.
Users consistently report contract lock-ins that make cancellation difficult, surprise renewal charges, and features that cost extra even though they should be standard. One customer reported being charged for a second year without consent after explicitly declining renewal.
| Cost Element | Venvera | Vanta |
|---|---|---|
| Base platform (annual) | All frameworks included | $10,000–$15,000 (1 framework) |
| Each additional framework | $0 | ~$5,000/year |
| 5 frameworks (DORA + GDPR + ISO + NIS2 + AI Act) | Included in every plan | $30,000–$50,000+ |
| External auditor access | Unlimited, built-in | Additional user seats |
| Pricing transparency | Published on website | Requires sales calls |
| Contract flexibility | Flexible terms | Annual lock-in, difficult cancellation |
The Bottom Line on Pricing
An EU financial entity needing DORA, GDPR, ISO 27001, NIS2, and the EU AI Act would pay Vanta $30k–$50k+/year just for framework fees. With Venvera, all 10 frameworks are included from day one at a fraction of the cost. No surprises, no "let me check with my manager" pricing calls.
Comparison 2
DORA Compliance: Purpose-Built vs. Bolted-On
The Pain
DORA is the most complex EU regulation to hit financial services in a decade. It requires a Register of Information, ICT provider risk management, resilience testing programs, and incident classification with NCA reporting — all with specific data structures and export formats. Vanta announced "DORA support" in late 2024, but that means a control checklist you can map evidence against. That's not a compliance platform — that's a spreadsheet with better CSS.
What Venvera provides that Vanta doesn't:
Register of Information (Art. 28)
Full RoI module with ICT providers, contractual arrangements, business functions, risk assessments, branches, and sub-outsourcing chains.
XBRL & CSV Regulatory Export
Built-in XBRL and CSV export in ESA format — exactly what supervisory authorities expect when they request your register.
ICT Third-Party Risk Management
DORA-specific TPRM with concentration risk analysis, exit plans, sub-outsourcing tracking, and CTPP classification.
Resilience Testing Program
Full lifecycle: TLPT, scenario-based testing, vulnerability assessments, findings tracking, and remediation management.
Incident Classification (DORA-Specific)
Article 18 severity classification with NCA reporting timelines (4h initial, 24h intermediate, 72h final), root cause taxonomy.
ESA Entity Codes & Classifications
All ESA reference codes built in: LEI validation, entity types, NCA identifiers, currencies, countries, and ICT service taxonomies.
| DORA Requirement | Venvera | Vanta |
|---|---|---|
| Register of Information (Art. 28(3)) | ✓ Full module | ✗ Not available |
| XBRL/CSV regulatory export | ✓ ESA format | ✗ Not available |
| ESA entity codes & classifications | ✓ All codes built-in | ✗ Not available |
| ICT third-party risk management | ✓ DORA-specific TPRM | ~ Generic vendor management |
| Resilience testing program (TLPT) | ✓ Full lifecycle | ✗ Not available |
| Incident classification (Art. 18) | ✓ Auto-classification + deadlines | ~ Generic incident tracking |
| Concentration risk analysis | ✓ Automated | ✗ Not available |
| Gap assessment with DORA articles | ✓ Article-by-article | ~ Generic control mapping |
Why This Matters
When your NCA requests your Register of Information in XBRL format, Vanta won't help you. When you need concentration risk analysis across your ICT providers, Vanta won't help you. When you need to track TLPT engagements with findings-to-remediation traceability, Vanta won't help you. Venvera was designed for this from the ground up.
Comparison 3
Cross-Framework Control Crosswalk
The Pain
A single "encryption at rest" control satisfies requirements in DORA, NIS2, ISO 27001, SOC 2, NIST CSF, and GDPR simultaneously — but most platforms make you implement and evidence it six separate times. Research shows organisations managing 3+ frameworks spend up to 90% of compliance effort on duplicate work.
Venvera's Control Crosswalk maps 38 control domains across all frameworks in a single interactive matrix. Implement a control once, and every framework that requires it lights up green. No duplication, no missed mappings, no spreadsheets.
🔍 Live Status
Each cell pulls real-time compliance data — implementation status for control frameworks and assessment scores for gap frameworks.
📈 Coverage Analytics
Per-framework coverage percentages, compliant/partial/gap breakdowns, and drill-down to individual control references.
🔎 Smart Filtering
Filter by domain (encryption, access control, incident management), by status (compliant, partial, gap), or by framework.
📱 Responsive Matrix
Desktop shows the full grid with framework columns; mobile collapses to card-based layout with status indicators. Works everywhere.
| Cross-Framework Feature | Venvera | Vanta |
|---|---|---|
| Multi-framework control matrix | ✓ 38 domains × 10 frameworks | ~ Basic SOC 2/ISO mapping only |
| Live implementation status per cell | ✓ Real-time from assessments | ✗ Not available |
| Implement once, satisfy many | ✓ Automatic propagation | ✗ Manual per framework |
| Gap identification across frameworks | ✓ Auto-detected | ✗ Not available |
| EU regulation coverage (DORA, NIS2, AI Act) | ✓ Full mapping | ✗ Not mapped |
Competitive Advantage
Vanta and Drata offer basic SOC 2/ISO mapping, but neither provides live, multi-directional crosswalking across EU regulations like DORA, NIS2, and the AI Act. This capability is unique to Venvera — and it eliminates up to 90% of duplicate compliance work.
Comparison 4
Compliance Health Score: One Number, Every Framework
Executives and board members don't want to wade through framework-specific dashboards. They want one number that tells them: "Are we compliant?"
Venvera's Compliance Health Score delivers exactly that — a unified 0–100 score with letter grades (A through F) per framework and an overall weighted score across all enabled regulations.
Four-Signal Scoring Model
40%
Gap Assessment
Primary signal from formal questionnaire assessments across all frameworks.
30%
Control Implementation
ISO controls, SOC 2 criteria, NIST subcategories, RoI completeness, processing activities.
15%
Operational Health
Open incidents, incident resolution rate, overdue items, task completion rates.
15%
Policy Coverage
Approved vs total policies, overdue reviews, documentation gaps.
The overall score uses framework-weighted averaging that reflects regulatory complexity: DORA (20%) and ISO 27001 (18%) carry more weight than simpler frameworks, ensuring the score accurately reflects your true compliance posture.
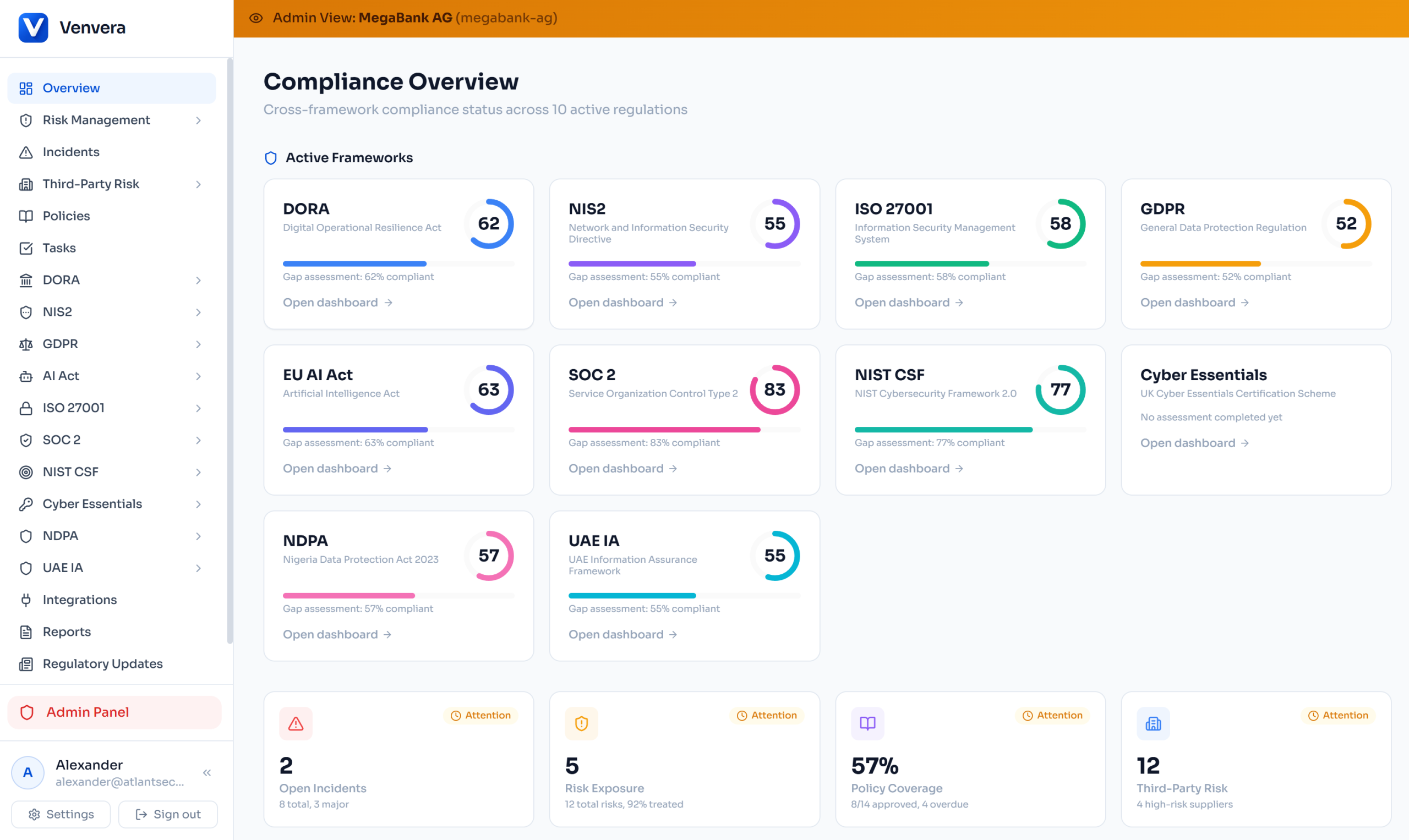
Dashboard Integration
The health score banner appears at the top of the main dashboard showing the overall grade ring alongside clickable per-framework score badges. One glance tells the full story. Each badge links to the relevant framework dashboard for drill-down. Board members and executives see this first — no deep-diving required.
Comparison 5
Multi-Framework Incident Classification Engine
The Pain
A single cybersecurity incident can trigger reporting obligations under DORA (4-hour deadline), NIS2 (24-hour early warning), GDPR (72-hour breach notification), and the AI Act simultaneously. Missing even one deadline carries penalties up to €20 million. Manual classification across four regulatory frameworks during a crisis is a recipe for failure.
Venvera's classification engine analyses incident attributes and automatically determines which regulations are triggered, what the classification is under each framework, and exactly when each reporting deadline falls.
Four Frameworks, One Analysis
DORA — Article 18
Evaluates 7 impact criteria. Two+ triggers = Major classification with automatic ITS deadlines: 4h initial, 24h intermediate, 72h final, 30-day root cause.
NIS2 — Article 23
Assesses 6 criteria including operational disruption, financial loss (>€500K), cross-border impact. Triggers 24h early warning, 72h notification, 30-day final report.
GDPR — Article 33/34
Determines if the incident is a personal data breach. Evaluates sensitive data categories, scale of impact, vulnerable groups. Distinguishes reportable from high-risk breaches.
AI Act — Article 62
Identifies AI system involvement, fundamental rights impact, and potential for serious harm. Cross-references with AI system registry for 72h market surveillance notification.
| Incident Management | Venvera | Vanta |
|---|---|---|
| Multi-framework auto-classification | ✓ DORA + NIS2 + GDPR + AI Act | ✗ Single framework only |
| Automatic reporting deadline calculation | ✓ Per framework, per deadline | ✗ Not available |
| Confidence scoring on classification | ✓ High / Medium / Low | ✗ Not available |
| NCA authority report generation | ✓ PDF export | ✗ Not available |
| Re-analysis as details evolve | ✓ One-click reclassify | ✗ Not available |
Why This Matters
During a real incident, teams are scrambling. They shouldn't also be reading four different regulatory texts to determine reporting obligations. Neither Vanta nor Drata offers multi-regulation incident classification. Venvera does it instantly, with criterion-by-criterion justification and legal basis references.
Comparison 6
Vendor Questionnaires with Secure Access Codes
DORA requires financial entities to assess ICT third-party risk — which means sending security questionnaires to every vendor, collecting their responses, and tracking completion. Venvera makes this seamless with a built-in vendor questionnaire portal.
🔒 6-Digit Access Codes
Vendors receive a unique link + 6-digit access code for security. Prevents unauthorized access even if the link is shared.
⏱️ Expiring Links
Questionnaire links expire after a configurable period. Status tracking shows pending, in progress, completed, or expired.
📝 Dynamic Questions
Multiple question types (yes/no, text, select, N/A) grouped by category with real-time validation and progress tracking.
📊 Auto Risk Classification
Vendor risk is automatically classified based on questionnaire responses. No manual scoring needed.
Vendors see a clean, standalone portal — no login required, no app installation. They answer the questions, upload evidence if needed, and submit. Your team sees completion status, risk scores, and flagged responses in the TPRM dashboard.
| Vendor Assessment | Venvera | Vanta |
|---|---|---|
| Secure vendor portal with access codes | ✓ Built-in, code-protected | ~ Vendor risk management (add-on) |
| No vendor login/account required | ✓ Link + code access | ✗ Requires vendor account |
| Auto risk classification from responses | ✓ Automatic scoring | ~ Manual risk assessment |
| DORA-specific TPRM integration | ✓ Linked to RoI & exit plans | ✗ Generic vendor management |
Comparison 7
Features Vanta Simply Doesn't Have
Beyond the major modules above, Venvera ships capabilities that don't exist anywhere in Vanta's platform — because they were designed for the EU regulatory reality that Vanta wasn't built to address.
🇪🇺 NIS2 National Transposition Tracker
NIS2 is a directive, not a regulation — each EU member state transposes it differently. Germany's NIS2UmsuCG adds CEO personal liability. Italy introduces criminal sanctions. France combines NIS2 with CER. Venvera tracks transposition across 27+ EU member states with status, national law names, supervisory authorities, penalty ranges, and key national differences.
Vanta: Not available. No country-level NIS2 tracking.
⚠️ Officer Liability Tracking
Under DORA and NIS2, senior management can be held personally liable for compliance failures. Venvera's board dashboard tracks officer liability status (compliant/at-risk/non-compliant) with framework-specific alerts when management obligations are unmet.
Vanta: Not available. No personal liability tracking.
🤖 AI-Powered Policy Generation
Select a policy template from any of your enabled frameworks (DORA, NIS2, ISO 27001, GDPR, AI Act, SOC 2, NIST CSF) and Venvera's AI generates a complete policy draft pre-filled with your organisation's data — jurisdiction, entity type, frameworks, and company profile. Then manage the full lifecycle: draft, review, approval, versioning.
Vanta: Basic policy templates without AI generation or company-specific prefilling.
📈 Risk Management with Snapshots & Appetite
Full ICT risk register aligned with DORA Article 6: inherent/residual risk scoring, 5×5 likelihood/impact heatmap, risk appetite thresholds (accept/treat/escalate), treatment plans with control mapping, and point-in-time risk snapshots that capture your risk profile for historical comparison and audit evidence.
Vanta: Basic risk register with limited customisation. No appetite thresholds, no snapshots.
📄 One-Click Board Reports (DOCX)
Generate executive-level compliance reports for any framework — or a unified report across all frameworks — with a single click. Reports include compliance scores, risk metrics, incident trends, policy status, and remediation progress. Exported as formatted DOCX ready for board presentation. Auditors can generate these self-service.
Vanta: Manual report assembly. No multi-framework unified report.
| Unique Feature | Venvera | Vanta |
|---|---|---|
| NIS2 transposition per EU country | ✓ 27+ countries tracked | ✗ Not available |
| Officer liability dashboard | ✓ DORA & NIS2 liability status | ✗ Not available |
| AI policy generation (company-prefilled) | ✓ Multi-framework templates | ~ Basic templates, no AI gen |
| Risk snapshots for audit evidence | ✓ Point-in-time capture | ✗ Not available |
| Risk appetite thresholds | ✓ Configurable per org | ✗ Not available |
| One-click board reports (DOCX) | ✓ Per framework + unified | ✗ Manual assembly |
| GDPR DSAR tracking | ✓ Full lifecycle | ✗ Not available |
| EU AI Act system inventory & GPAI | ✓ Classification + conformity | ~ Basic AI Act controls |
| Regulatory updates feed | ✓ Curated, framework-tagged | ~ General updates |
Comparison 8
10 Frameworks, Zero Add-On Fees
European financial entities don't have the luxury of single-framework compliance. DORA, GDPR, NIS2, ISO 27001, and increasingly the EU AI Act all apply simultaneously — with overlapping but distinct requirements. Vanta treats each framework as a separate paid module. Venvera includes everything.
| Framework | Venvera | Vanta |
|---|---|---|
| DORA | ✓ Deep, purpose-built | ~ Control checklist |
| GDPR | ✓ ROPA, DPIAs, DSRs, breaches, DPAs | ~ Basic controls |
| ISO 27001 | ✓ Full ISMS with Annex A | ✓ Strong support |
| NIS2 | ✓ Assessments, training, KPIs | ~ Basic controls |
| EU AI Act | ✓ Systems, conformity, GPAI, oversight | ~ Recently added, basic |
| SOC 2 | ✓ Full TSC coverage | ✓ Core strength |
| NIST CSF | ✓ Included | ✓ Included |
| Cyber Essentials (UK) | ✓ Included | ✗ Not available |
| NDPA (Nigeria) | ✓ Included | ✗ Not available |
| UAE IA | ✓ Included | ✗ Not available |
Cross-Framework Control Mapping
Venvera automatically maps controls across all frameworks. Implement "encryption at rest" once, and every framework that requires it — DORA, ISO 27001, NIS2, SOC 2, NIST CSF, GDPR — lights up green. Research shows organisations managing 3+ frameworks spend up to 90% of compliance effort on duplicate work. Venvera eliminates this. Vanta treats frameworks as separate silos.
Comparison 9
Data Sovereignty: Europe vs. San Francisco
The Conflict
Vanta is a San Francisco-based company. Your compliance data — risk assessments, incident reports, vendor contracts, potentially GDPR-protected personal data — is processed through US infrastructure. For EU financial institutions subject to DORA and GDPR, this creates a fundamental irony: using a US-based platform to manage your EU regulatory compliance introduces the very third-party risk these regulations are designed to control.
DORA Art. 28–30
Requires financial entities to manage ICT third-party risk, including data location and jurisdictional considerations.
GDPR Chapter V
Governs international transfers of personal data. Compliance data often contains personal information subject to these rules.
| Data & Infrastructure | Venvera | Vanta |
|---|---|---|
| Data hosting location | Amsterdam, EU | United States |
| Company jurisdiction | European | United States |
| Transatlantic data transfers | ✓ None required | ✗ Required |
| Subject to US surveillance laws | ✓ No | ✗ Yes (CLOUD Act, FISA) |
| Backup storage | EU, AES-256 encrypted | US-based infrastructure |
Comparison 10
Security Architecture: Defense in Depth
Your compliance platform contains your organisation's most sensitive operational data. The security architecture behind that platform determines whether a single vulnerability can compromise everything — or nothing.
We can't speak to how Vanta protects data internally — their architecture isn't publicly documented at that level. What we can do is be transparent about what Venvera provides:
| Security Layer | Venvera |
|---|---|
| Tenant data isolation | PostgreSQL Row-Level Security — enforced by the database engine, not application code |
| Defense layers | Edge middleware + API route guards + Database RLS (3 independent layers) |
| File encryption | AES-256-GCM with per-tenant encryption keys |
| Audit logging | Append-only, tamper-evident audit trail |
| Authentication | Azure AD SSO — no passwords stored, no credential databases to breach |
| Access control | RBAC + per-user group permissions + per-framework access gating |
| Infrastructure hardening | fail2ban, UFW firewall, auditd, hardened SSH, automated encrypted backups |
| SSRF & injection prevention | Webhook URL validation, parameterised queries, HTML escaping, CSRF tokens |
Database-Level Isolation
Venvera's Row-Level Security means tenant isolation is enforced by the database engine itself. Even if a software bug existed in the application layer, the database would prevent cross-tenant data access. This is the same isolation pattern used by regulated financial infrastructure. We believe this is a stronger guarantee than application-level isolation — but we encourage you to ask any vendor, including Vanta, to explain exactly how they isolate tenant data.
Comparison 11
External Auditor Access: Built for Real Audits
External audits are a core part of compliance. Your Big Four auditor, your NCA inspector, your ISO certification body — they all need to see your data. With Vanta, you share your screen, export PDFs, or pay for additional user seats with access controls that weren't designed for external parties.
Venvera's auditor access is a first-class feature:
Two-Factor Magic Link Auth
No SSO account needed. Email magic link + 6-digit code shared via separate channel. Prevents link sharing.
Strictly Read-Only
Enforced at the middleware level, not just the UI. Auditors can view everything and generate reports but can't modify a record.
Time-Limited Sessions
7 to 90 days, configurable per auditor. Access expires automatically — no forgotten accounts lingering for months.
Instant Revocation
Admin clicks "Revoke" and access terminates immediately. Full audit trail of every page the auditor visited.
| Auditor Capability | Venvera | Vanta |
|---|---|---|
| Dedicated auditor access | ✓ Built-in feature | ✗ Requires paid user seat |
| No SSO/account required | ✓ Magic link + code | ✗ Needs account setup |
| Auto-expiring sessions | ✓ 7–90 days configurable | ✗ Manual management |
| Report generation for auditors | ✓ Self-service | ~ Manual export/share |
| Additional cost per auditor | $0 | Per-seat fee |
Comparison 12
Integrations: Workflow vs. Evidence Collection
Vanta's integration story is primarily about evidence collection — connecting to AWS, GitHub, Okta to automatically gather audit evidence. Useful for SOC 2, but it doesn't address how compliance work actually flows through an organisation.
Venvera approaches integrations differently — focusing on workflow integration that makes compliance part of how your teams already operate:
Jira Task Sync
Push compliance tasks to Jira, receive status updates automatically. Engineering works in Jira; compliance stays current in Venvera.
Slack & Teams Notifications
Real-time compliance events — new tasks, incidents, scan results — delivered where your team already communicates.
Azure Cloud Scanning
Automatically discover and assess your Microsoft cloud infrastructure against compliance requirements.
Custom Webhooks (HMAC-Signed)
Connect Venvera to any system with cryptographically signed webhook payloads. Full delivery monitoring and retry logic.
| Integration Type | Venvera | Vanta |
|---|---|---|
| Jira bi-directional sync | ✓ Push + receive updates | ~ One-way ticket creation |
| Slack/Teams webhooks | ✓ Rich event notifications | ✓ Slack integration |
| Custom HMAC-signed webhooks | ✓ With delivery monitoring | ✗ Not available |
| AI compliance assistant | ✓ Grounded in your data | ~ AI agent (mixed user reviews) |
| Board report generation | ✓ One-click, multi-framework | ~ Manual assembly |
Comparison 13
User Experience: What Real Users Say About Vanta
Across Capterra, G2, Gartner Peer Insights, and TrustRadius, Vanta users consistently flag the same issues:
Unintuitive Interface
Users report confusing navigation, bugs affecting usability, and delays in UI updates reflecting completed tasks.
Manual Effort Still Required
Despite "automation" claims, users report significant manual work. Automation depth falls short as compliance needs mature.
AI Quality Concerns
Some reviewers on G2 and Capterra describe Vanta's AI features as "underwhelming" with inconsistent output quality.
Support Challenges
Users report difficulty reaching support teams and the absence of direct contact methods like phone numbers.
Venvera was built by a team that has spent years in EU compliance:
Single Dashboard
Real-time compliance scores across all frameworks. One view, every regulation. No tab-switching between siloed modules.
Cross-Framework Tasks
One task list with framework assignments, priority levels, assignees, and team workload views. Auto-generated from assessments.
Dark Mode
For the compliance analyst still working at 10pm. Full dark theme across every module — not an afterthought.
European Defaults
DD/MM/YYYY dates, EU regulatory terminology, DORA-first navigation. Built for how European compliance teams actually work.
The Full Picture
A side-by-side comparison across every dimension that matters for EU financial entity compliance.
| Category | Venvera | Vanta |
|---|---|---|
| Built for | EU financial entities | US tech startups |
| DORA support depth | RoI, XBRL, TPRM, resilience testing | Control checklist |
| Frameworks included | 10, all included | Pay ~$5k per framework |
| Cross-framework mapping | Automatic, live | Manual / siloed |
| Data location | Amsterdam, EU | United States |
| Tenant isolation | Database-level RLS | Not publicly documented |
| Auditor access | Built-in, unlimited, 2FA | Paid user seats |
| Regulatory export | XBRL, CSV (ESA format) | PDF/CSV only |
| Pricing transparency | Published | Requires sales calls |
| Security architecture | RLS + 3-layer defense-in-depth | SOC 2 Type II certified |
Ready to see the difference?
10 compliance frameworks, purpose-built DORA tooling, European data sovereignty, unlimited auditor access, and transparent pricing — all from day one.
Venvera is built by Atlant Security in Amsterdam. This comparison is based on publicly available information, vendor documentation, and third-party review platforms (Capterra, G2, Gartner Peer Insights, TrustRadius) as of March 2026. Pricing data sourced from independent reviews and user reports. Where Vanta's internal architecture or capabilities are not publicly documented, we have noted this rather than speculating. Vanta is a trademark of Vanta, Inc. We encourage prospective buyers to evaluate both platforms directly.